Where are our tech ninjas?
The first quarter of 2019 was quite stirring. We have also published several articles about our work. So, let’s start just by thinking about these developments:
Also, what happened in Q2?
The contrast is huge… Well, our tech ninjas thought have a little rest after the Cloudfest exhibition. Haha, just kidding… 🙂 Actually, the opposite happened. They worked harder than ever before. Also, we were so busy that we haven’t even had time to share release notes, but our hard work has had some great results too.
However, it’s better later than never, so I’d like to sum up what happened ACTUALLY in Q2.
We are happy to introduce you to our new colleague, Zsolt Varga, who joined as a Product Manager to our ninjastic team in spring.

In 2002, when he was 14 years old, he fell in love with coding. He met with HTML that year and in less than a week, he had a running website. He kept learning and became familiar with PHP and JavaScript very soon. The result of his passionate work was 250k visitor/month on his little website.
In his early 20’s he took his hobby and turned into a job and worked with many smaller firms. During this time, he developed many different ERP systems and became an enthusiastic team leader. He worked as a CTO at a software development company. Now, he is the Product Manager of BitNinja since spring this year (2019).
A fun fact about Zsolt: He is a llama-lover, so that’s why we surprised him with Carl. Look at how happy he is about his llama:

Zsolt always wants more, so he never stops learning new things. Thanks to him, we can improve our agile software development skills. So, in the future, there will be more user interviews to develop that, what our customer need and make it quicker than ever. In this article you can see, that we are already on the road, where we want to be, as we released more developments in 2019 Q2 compared to every other previous quarter.
In our Ninja HQ, the most important is to keep our partners’ servers safe and provide the most convenient and most powerful service. We are not just saying, but we really believe in customer-driven development. Therefore, when we say that customer is the first, we really mean it. So we work hard every day to prove that we are worthy of being called the best server security service. The feature requests made by customers and all of the feedback have been really useful for us – so I’d like to say thank you, everyone, who help our work.
Of course, besides improving our internal work processes to make our ninjas’ daily work more efficient, we have been implementing some of our goals during our developments to provide better service for you every day:
Let’s see how we achieved these goals in Q2!
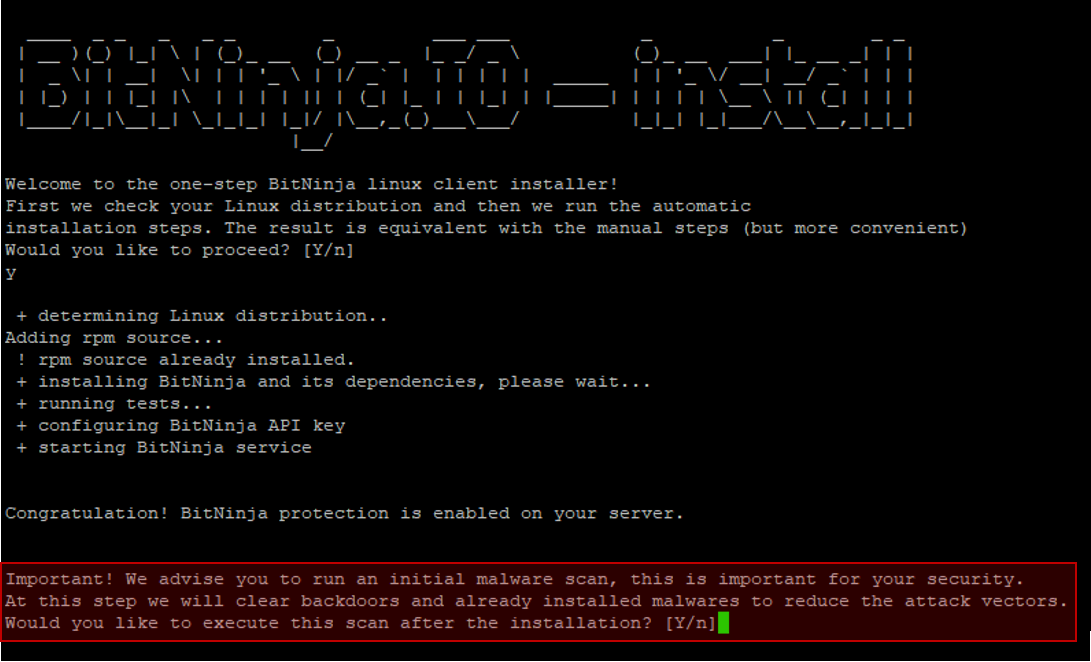
I’ve already talked about the importance of the manual malware scan. Also, just to make sure that you won’t forget about starting this manual scan, we offer to clean your server for you, as soon as you’ve installed the agent on the server. You can start a scan after you run the installation code in CLI, with a simple click.
Our real-time Malware Detection module watches every file changes. Not only that, when it finds an infected file, the Defense Robot will try to find and block the attacker IP. If you missed how our Defense Robot works actually, you can read about it in the article here.
We saw that when there is a malware found in a server, there are usually other infected files on the document root of the web site, which were uploaded earlier. Besides, to detect these files too, an automatic scan will start to the affected folder, when the Defense Robot has the information about this incident.
BitNinja puts the proactive protection in focus and our purpose is to stop the cyber attack at the very first step of the attack cycle. Those modules, which support this mission, became so mature, that we felt there is an odd-one-out protection module in our feature list. This is the Outbound WAF which has been beta for a long time now.
Recently, we identified a few problems that this module is currently causing. Also, since it can’t provide the stable protection that we want to offer to our partners, we decided to remove the OWAF from our feature list for a while. Right now, we are focusing on improving the other modules and create new (most powerful) features. Later, we’ll continue to develop the Outbound WAF too and make it mature too. However, until then this module is only available to those, who are still running it.
At the end of March, we discovered a new type of attack flood. We named it Hexa botnet and it is using special techniques to attack WordPress sites. The Post data shows only hexadecimal characters because of the hex coding. So, instead of only „simply” filtering for an exact expression, we needed to implement behavior-based rules into our Malware Detection and WAF module.
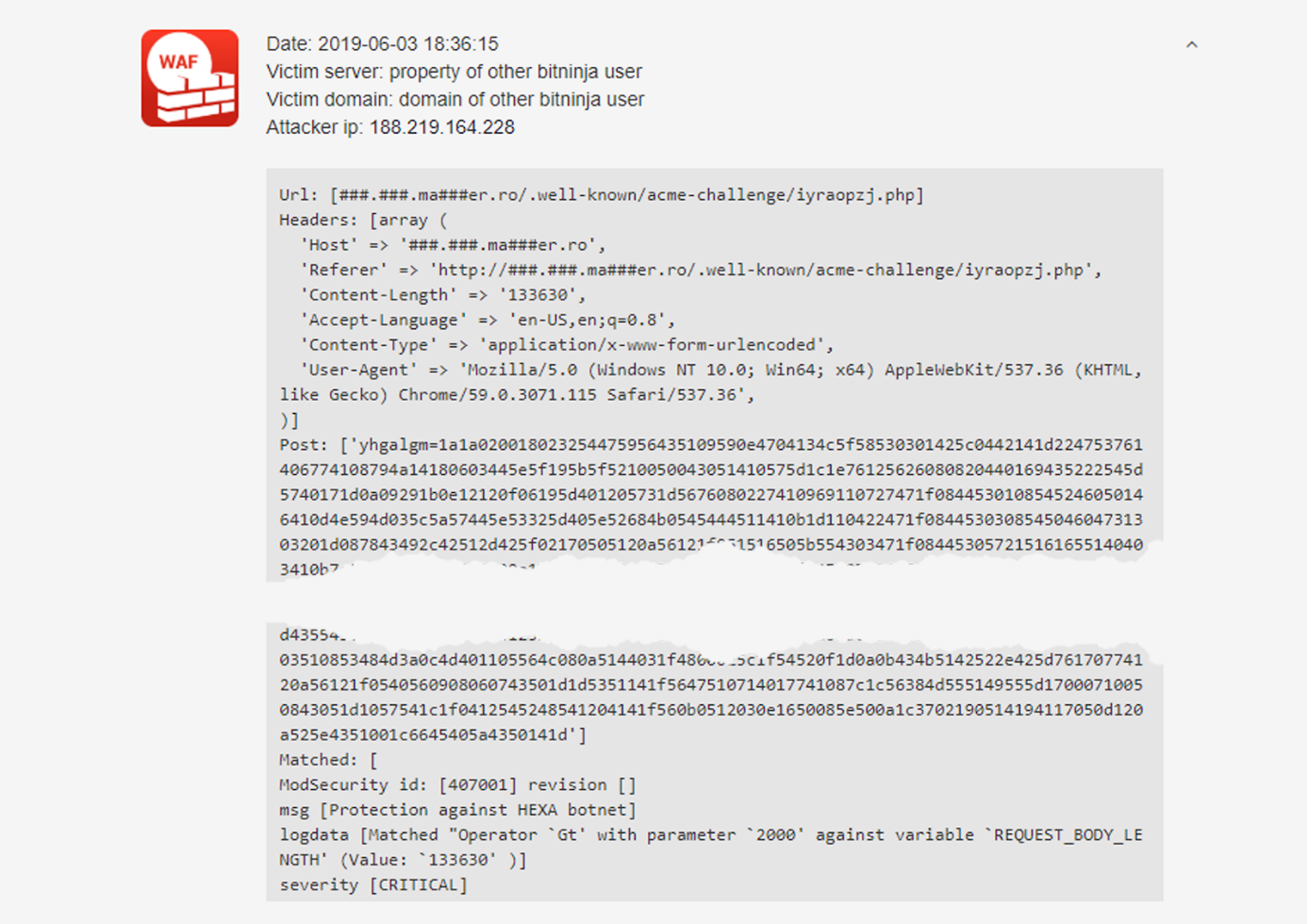
If you’d like to learn more about Hexa botnet, you can check it out in our previous article.
One customer asked us to fine-tune the OWASP CRS 941100 and 941160 rules when our WAF receives a Magento/Typo3 backend request. So, we made it! When the users edit the content in their admin, they won’t be falsely blocked thanks to our 1040001 and 1040002 rules.
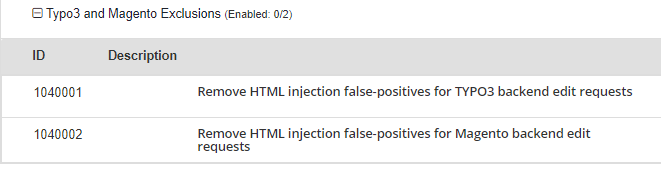
These rules are not applied to any of the BitNinja rulesets (as it was requested by a user for special cases). So, if you’d like to use them too, you need to enable manually.
The GeoIP database isn’t supported anymore, so we changed it to GeoIP2. Thanks to this, the fetched country information from the IP will be more accurate and up-to-date. What’s more, it’ll work with IPv6 IPs too (which is another project we are working on).
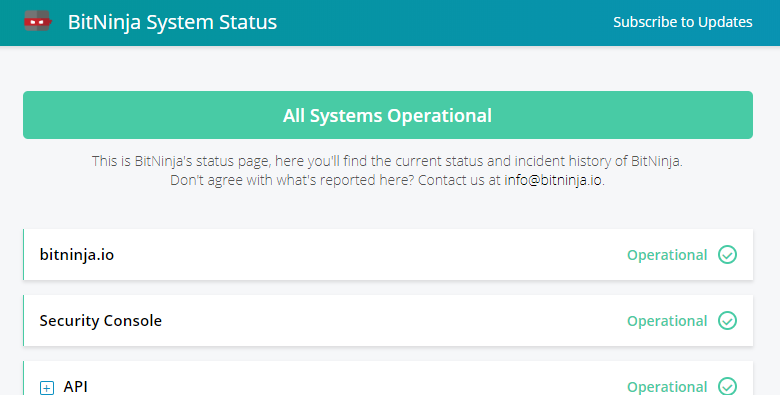
We understand how annoying it is when a service is not available for some reason. It’s always good to know what the problem actually, which part of the service is unavailable and why it is happening. That’s why we created a system status page, where you can check anytime the status of BitNinja:
We released a new beta module, called Trusted Proxy, which will allow blocking attacks coming from proxies. But, why is this module better than the previous approach?
Before the Trusted Proxy, BitNinja globally whitelisted the most popular CDNs (like CloudFlare, MaxCDN). However, unfortunately, the number of attacks coming through these proxies, increased so we need to do something to keep our partners’ servers safe. Also, we couldn’t whitelist every proxies worldwide. So, it might happen that an exit node’s thousands of users were blocked because of 1 user who sent malicious requests to BitNinja protected servers.
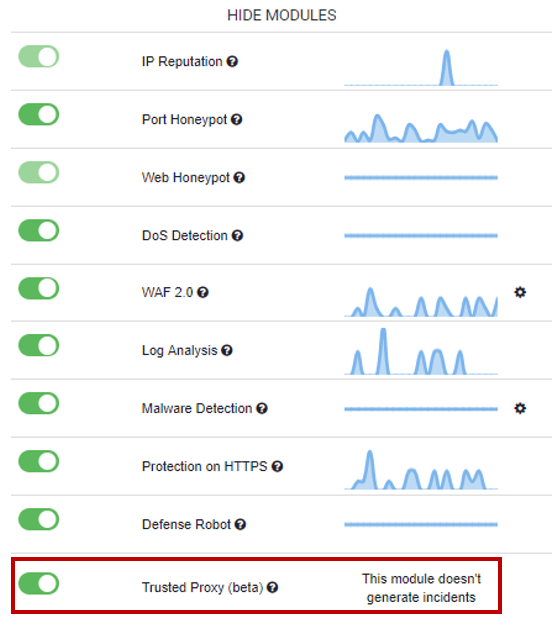
However, these times are now over. BitNinja, with the Trusted Proxy, can see not only the proxy IP but the source IP as well, which opened new ways to analyze the logs.
Please use this module with caution, as it’s in beta yet. We are still working on to make it perfect. 😉
Soon, there’ll be a separate menu on the Dashboard for managing the Trusted Proxy settings.
This feature is long-awaited, and gosh it was a tremendous job to deal with. Still, here we are with the first release candidate implemented. But, for now, it's only available with a change in the config. Of course, this release might have some flaws but it’s important for us to get feedback for it from our ninja friends. If you’d like to be one of those (our VIP group is already testing it in the past few weeks), who can try the IPv6 support. So, please contact us at info@bitninja.io and we’ll help you to make the above-mentioned changes in the config.
Now, you have the chance to get instant alerts about how BitNinja performs on your servers. Currently, you can get 2 types of notifications. But soon, we’ll be implementing more options. You can find more details about the Slack integration in this article.

Do you have some great ideas to improve BitNinja? We always happily accept feature requests and believe in the power of our great community. All of the feedback and requests are highly important to us, so we encourage everyone to share their ideas with us. Previously, we collected these wishes on our Wantoo page, but we have now moved to the Productboard Portal. The purpose is the same, it’s only the platform that is new. We think this platform offers a more user-friendly UI to follow up the process of the task. If there’s anything that you haven’t shared with us, this is your time! Submit your ideas on the Productboard Portal.
We carefully selected those malware signatures, which are publicly listed as malware. However, we met with some cases, when these well-known signatures caused a false positive too. Now, you have the option to label this falsely detected files and add them to whitelist, so our Malware Detection and Malware Scanner won’t quarantine again.
Use the following command for whitelisting the given file for malware detector:
[--module=MalwareDetection] [--whitelist-file=/absolute/path/to/file]
By checking an IP history on the Dashboard, you can see a BNVL label besides some of the incidents.
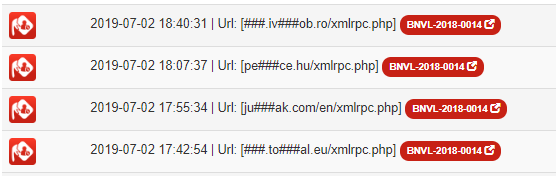
BitNinja Server Security's BNVL identifiers are intended for use to identify publicly known information security vulnerabilities in publicly released software packages. This project collected and analyzed attack information from the BitNinja network after the cluster analysis was performed by the AI-powered Attack Vector Miner. If you click on the label, you can read more details about the concrete attack type. So far, over 100 vulnerability types have been discovered with this project, which is why we decided to show you these details. For example, this is the BNVL-2018-0014 public page.
The Investigations menu of our doc site was enriched with a new section. It is helpful when a website is not loading properly when the BitNinja is running. In order to find the greylisted host, we wrote a script which you can check on our doc site.
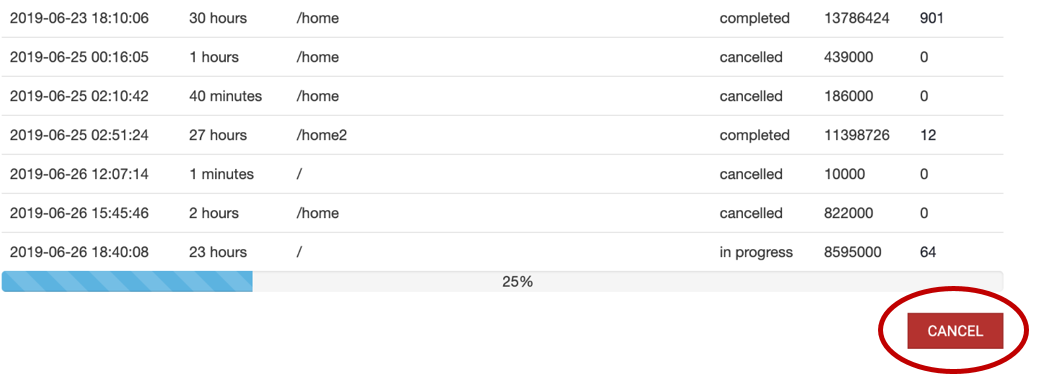
Rarely, but it happened that a malware scan process stuck on the Dashboard despite the fact that there was no active scan running on the server. We fixed this bug quickly, so the Malware Scan shows the correct process status.
As you know our WAF is an nginx reverse proxy, so it creates port redirections. Some parts of it needed a little improvement, and we also fixed some small iptables rules bugs too. Fortunately, only a few servers were affected by this bug.
In some special cases, our SSL Terminating module consumed too many resources. So, we needed to fix it quickly. Also, we made some correction with the cert handling, so collection old certs will be avoided in the future.
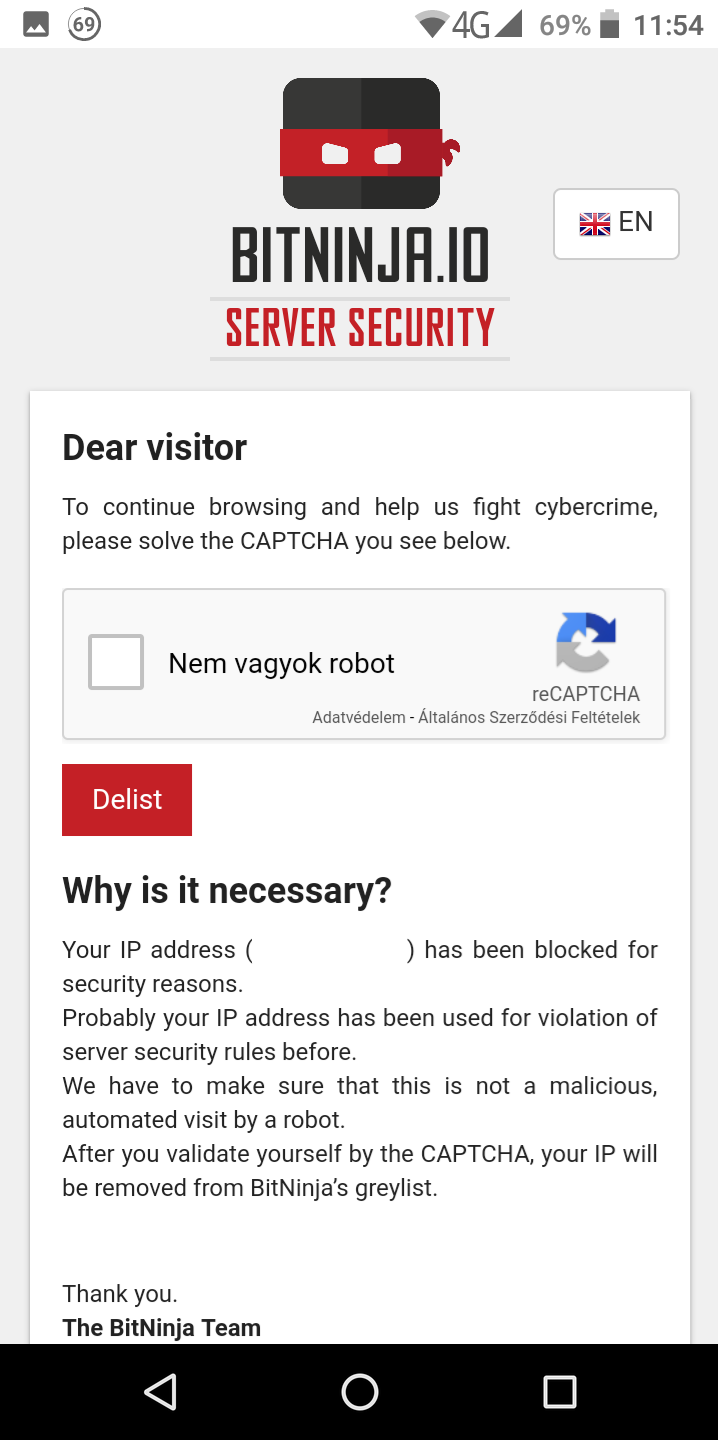
Nowadays, we know that browsing on smartphones is a daily thing, so we improved the responsivity of our CAPTCHA page when visited via mobile.
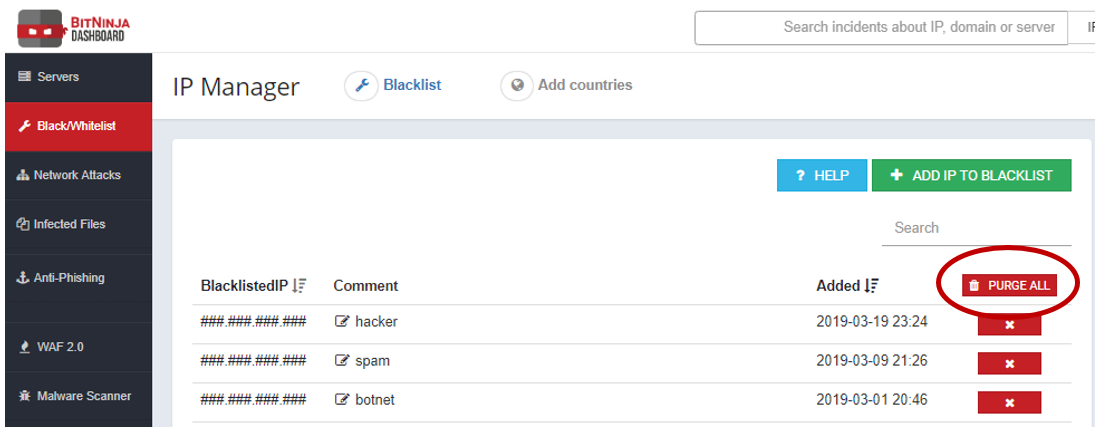
Would you like to remove all the IPs added to your black our whitelist? You can do it with one simple click because we have added a "Purge All" button to the Black/Whitelist menu as it already happened that we needed to purge a customer’s BL/WL from our database. So we thought it will be a useful feature on the Dashboard too.
If you visit the WAF settings, you can choose from 3 different BitNinja ruleset. Previously, they had different names. Here is how we changed them:
| Old name | New name |
| Safe minimum ruleset | Recommended |
| Medium ruleset | Medium risk |
| Strict ruleset | High risk |
Why was it necessary?
The old names were a bit misleading and some customers thought that the safe minimum ruleset offers a minimum protection level. Not only that it is better to enable the medium or strict ruleset for the default / pattern.
Unfortunately, this is actually the opposite of how our WAF should be used. The formerly called safe minimum ruleset contains those WAF rules, which can work properly on any kind of server and with any kind of CMS. We collected those rules into this ruleset, which have the lowest chance to cause false positives. That’s why we renamed it to Recommended ruleset to help our ninja friends to understand the behavior of these rulesets.
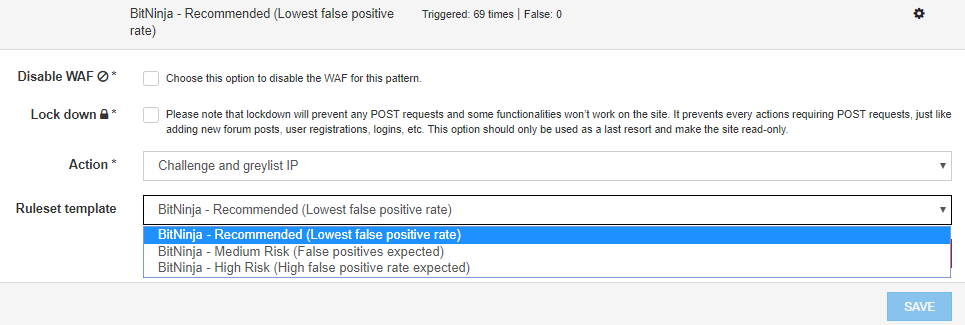
Applying the two other BitNinja ruleset is only recommended for specific domain patterns as they contain stricter rules, which can work only in special cases. Therefore, they can cause false positives sometimes and we are sure that you’d like to avoid false positives.
We have published an article series about How to use the WAF properly, so if you are still not confident about this topic, check out those articles. 😉 Or feel free to contact us at info@bitninja.io because we are always happy to help.
Now, if you start a manual scan from your Dashboard, you have the option to cancel the scan if it’s necessary.
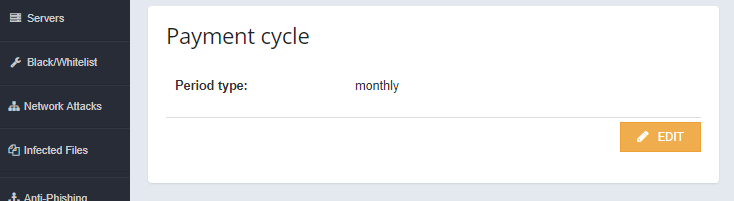
Many of our customers prefer to pay only once in a year for a BitNinja license. So if you are on a monthly payment cycle now and would like to pay yearly, then you don’t need to wait until we make the necessary changes for you. Instead, you can choose the appropriate period type under your payment settings.
Don’t worry if you switch from a yearly payment to monthly period, you won’t lose the remaining amount of paid your license. Instead, it’ll be added to your balance, so you can use it for the monthly charges.
We have already made some changes and we are also planning to add more options to show a clear picture of what’s going on your server. Now, if you visit the Infected Files menu, you can see the total detected malware count on the top:
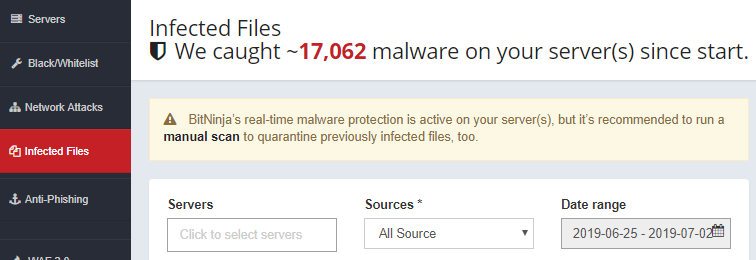
Note: the ~ character is there for one reason. This data is updated hourly, so it might happen that the accurate number is even higher than the number that appears at that moment. 😉
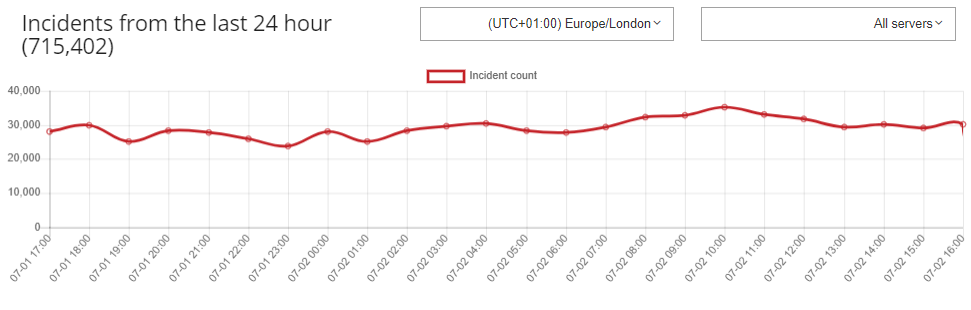
But there’s another new thing that most of you have probably already discovered if you’ve recently logged onto your Dashboard. In the Servers menu, you can see a chart which shows all the blocked requests on your BitNinja protected servers.
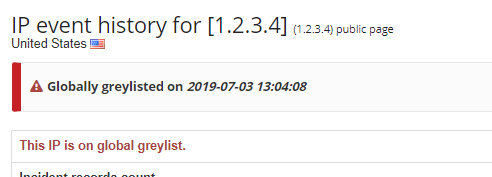
You could realize one more new information on your Dashboard. In the IP history, you can see immediately when the IP was added to our grey- or blacklist. Under this data, you can see a highlighted message about on which BitNinja list appears the IP.
There is always room for improvement and we have many ideas about how we could improve the UI/UX of our Dashboard. However, we know that a huge change and a completely new Dashboard would shock a lot of customers. That’s why we are making only small changes slowly but steadily.
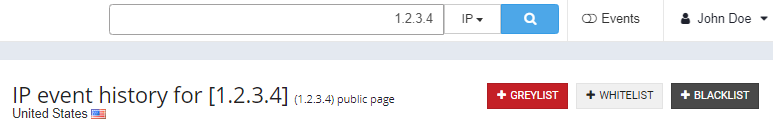
We unified the buttons and the color of the buttons are chosen more consciously. For example, the add/remove IP from different lists buttons have different colors now (previously they all were red):
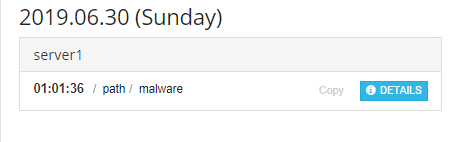
Another example: If you’d like to check the details of malware, now you can see a blue Details button instead of a small black magnifying glass icon (which wasn’t obvious, that is purposed to show more information about the malware).
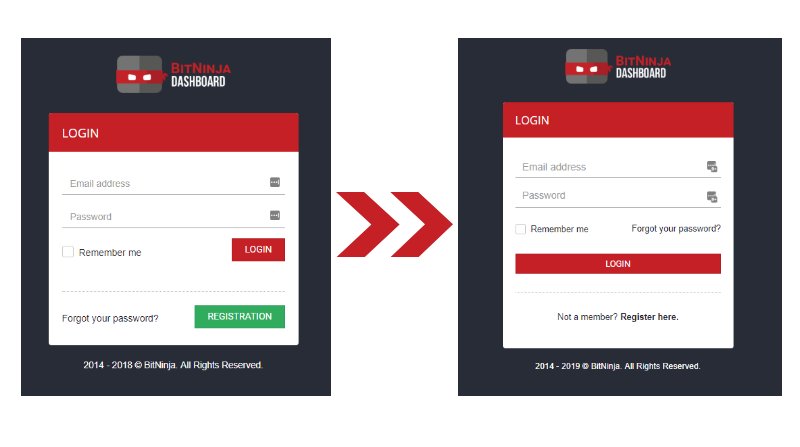
We have also made some small changes on our Login page as you can see the image below. There is a common login page appearance and the new login page helps people to find each function immediately.
It cannot be said enough, that setting up a password is how important if you’d like to keep your accounts safe. Also, I think most of you know how annoying is when you are choosing a password and you got a message that „the password needs to contain …” So, you add the requested character, but another message appears saying that „the password needs to contain …” Therefore, that’s why we have listed the requested steps in advance for setting up a strong password.
Besides these changes, we also made the payment settings page more responsive when visited from mobile or tablet and accelerated the Infected Files and WAF menus.
Our CAPTCHA page is available in many languages, however, our Browser Integrity Check (BIC) appeared in only 2 languages (English, Hungarian). Now, we implemented 11 new languages to provide a better user experience all around the world:
We are planning to add even more languages soon. Which language do you think we should implement first? Tell us in the comment section.
It’s not over! This is just the beginning of the quicker and more efficient developing cycles we are working on now. And what’s coming up? Here is a little spoiler:
Still, as we have received a huge number of great ideas from you guys – let me say thank you again for sharing your wishes with us, so there are many many other tasks we can choose from. 😉
You can check the feature request on our Productboard Portal. What would you like to have in BitNinja? Tell us in the comment section now. 😉




