The Kali Linux is an open source code operational system which is based in Debian. In the system we can find several „penetration” applications, such as:
In this article, I am going to tell you more about the Hydra’s operation and elaborate on how the BitNinja provides protection against it. Hydra works as a bruteforce program and it is one of the best password cracking tools in the world. It can be used with several protocols, like: HTTP, HTTPS, FTP, SMTP, SQL and CISCO.

In this article, I am going to perform password cracking on two servers, one of which is protected by BitNinja while the other one is not. First of all, for the attack we will need a good password list ( this is easy to obtain from the Internet ) After this we need to open Kali Linux and enter: Hydra. Now we are able to read a short description about its usage.
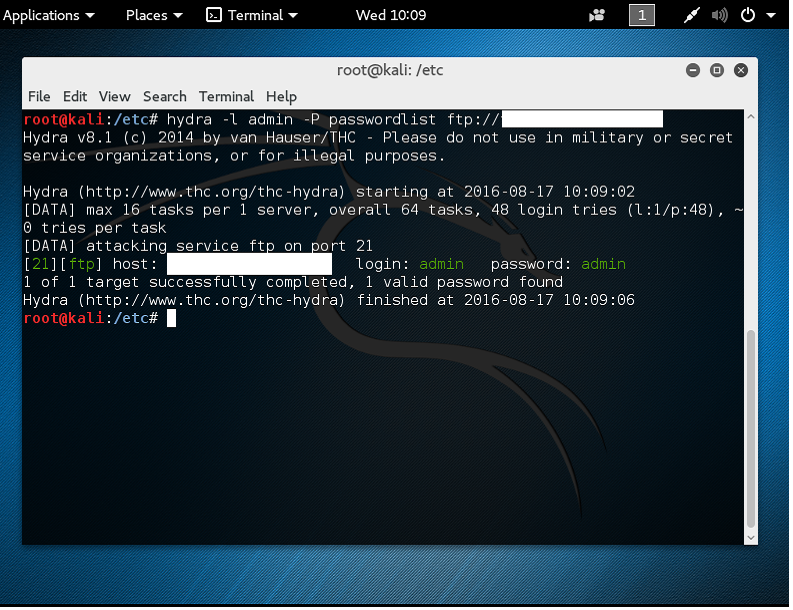
To attack an FTP account we need to use the following command:
hydra -l -P passwordlist ftp://
After some time we can see the results, in a „malicious” case the user-password pair.
As the attacked server is not protected by Bitninja, it is defenseless against unsolicited attempts. But let’s see what happens if we are attacking a server which has a through protection:
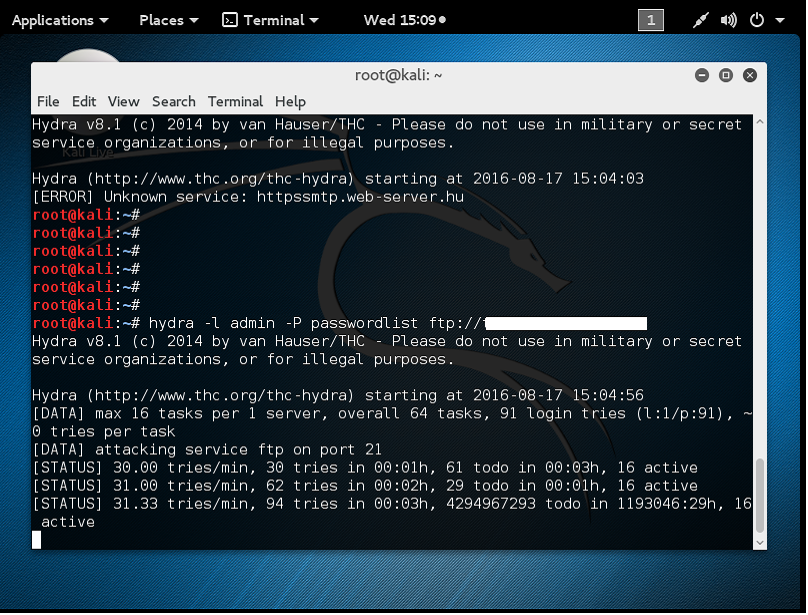
The attempt fails. On the admin.bitninja.io we can see the attacks coming from the attacker IP. In our example, we can see that someone tried to intrude into the account many times with a wring password. Firstly, the IP gets greylisted, then if the software experiences more incidents from the IP it will blacklist it. This way the hacker does not have a chance to crack the FTP gateway with bruteforce.
How did you like our article? Tweet your opinion, or share it with us on Facebook!




