In modern times websites are a key pillar for doing business. What looks appealing and engaging on the front end takes considerable effort to maintain on the backend. Treated as a commodity, these digital spaces are challenged every second of the day. The frontline of maintaining uptime plays out like this:
“We have performance issues on that server; its behavior is suspicious,” said John, the lead System Admin.
“Can you put someone on it right away from the Security team? We can’t afford a drop in performance to impact our customers. Support is already registering tickets, and we want to keep them to a minimum!" Says Jane, the CTO.
“Ok.” says John with a heavy sigh, “I will have to pull one of the team off of those new server deployments. It will take a few hours to clean, so I will book the extra overheads in the system.”
Sound familiar? The characters are fictitious, but the scenario is very real, and the consequential impact is detrimental to the business.
A day in the life of a hosting provider can swing like a clock pendulum from being uneventful when technology and process are ticking along nicely, to incidents that threaten to paralyze your operation.
More often than not, hosting providers will face security events that differ in severity; from minor ones contained and resolved in isolation, with minimal impact on your operational performance, to more severe incidents that can temporarily disrupt your business and that of your end customers.
Despite the level of severity, dealing with these breaches is a reactive task that requires an investment of time from your incident response teams.
Web Hosting is a highly competitive industry. Over time, the number of incidents followed by the laborious clean-ups can impact your company’s bottom line and put you at a competitive disadvantage.
With the Covid19 pandemic shifting staff to working remotely, cybercriminals have intensified their efforts, attacking social and technical vulnerabilities. According to several industry reports, it is likely that web hosting providers will continue to see an increase in the number of security incidents affecting them and their customers.
What is needed to combat this onslaught of malicious activity and keep your business healthy is further proactive measures than the ones you may already be taking today.
It starts with a proactive cybersecurity strategy that reduces your chances of being attacked in the first place, which we will cover today.
But first, let’s recap why cybersecurity is crucial for the web hosting industry.
Good cybersecurity is important for any business. But for web host providers, it’s essential.
Not only can cyberattacks cost you a fortune in regulatory fines and legal fees, but they can also destroy your reputation. Customers won’t use your services if you can’t safeguard their websites and sensitive data from threats.
In other words, cybersecurity is just as important for web hosts as…
Cyberattacks can prevent you from reaching these objectives, and you could fall behind your competitors. That’s why we will show you how to keep your systems protected by switching to a proactive mindset.
One of the most common mistakes companies make is to implement security tools as needed. When they discover a vulnerability, they purchase a solution to address that problem.
A better alternative to the ad hoc approach is to implement a cybersecurity framework that looks at prevention and threat response.
One of the most trusted frameworks in the industry is the NIST cybersecurity framework. The NIST framework acts as guidelines and best practices to help businesses strengthen their security posture in the face of an ever-changing threat landscape.
In the table below, we’ve created an adapter version of the NIST framework to suit the needs of web hosting providers.
The table’s been divided into…

Following this framework will help you develop a proactive strategy that focuses on preventative measures to keep you protected from threats.
About the reactive cybersecurity mindset.
A reactive cybersecurity strategy doesn’t look at the bigger picture. Instead of focusing on keeping systems protected from known and unknown threat vectors, it focuses exclusively on threat response. With a reactive approach, you only take steps when you realize the symptoms, such as high server load, resource usage, or blacklisted IPs.
CISOs following a reactive mindset would ask the following question: If we have this symptom, how do we respond?
Let’s see it through an example of a botnet attack how the reactive strategy works.
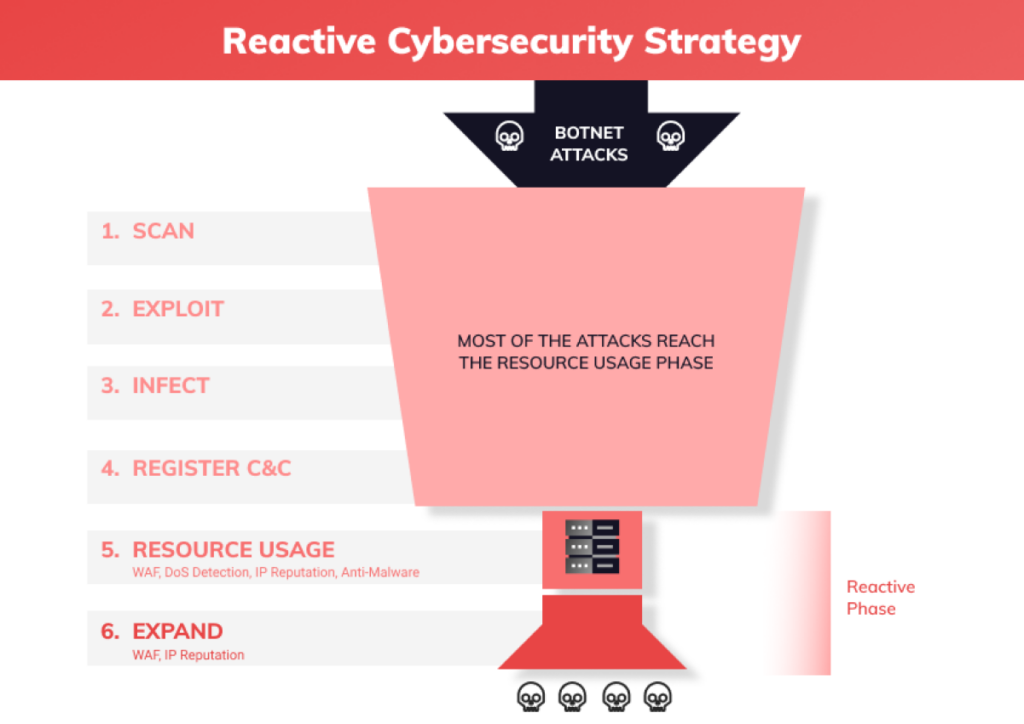
While this isn’t necessarily bad, reactivity is an incomplete cybersecurity strategy because it only focuses on responding to threats. Also, think about how you can protect your systems before an attack happens.
Having a proactive cybersecurity mindset means preparing for attacks before they happen.
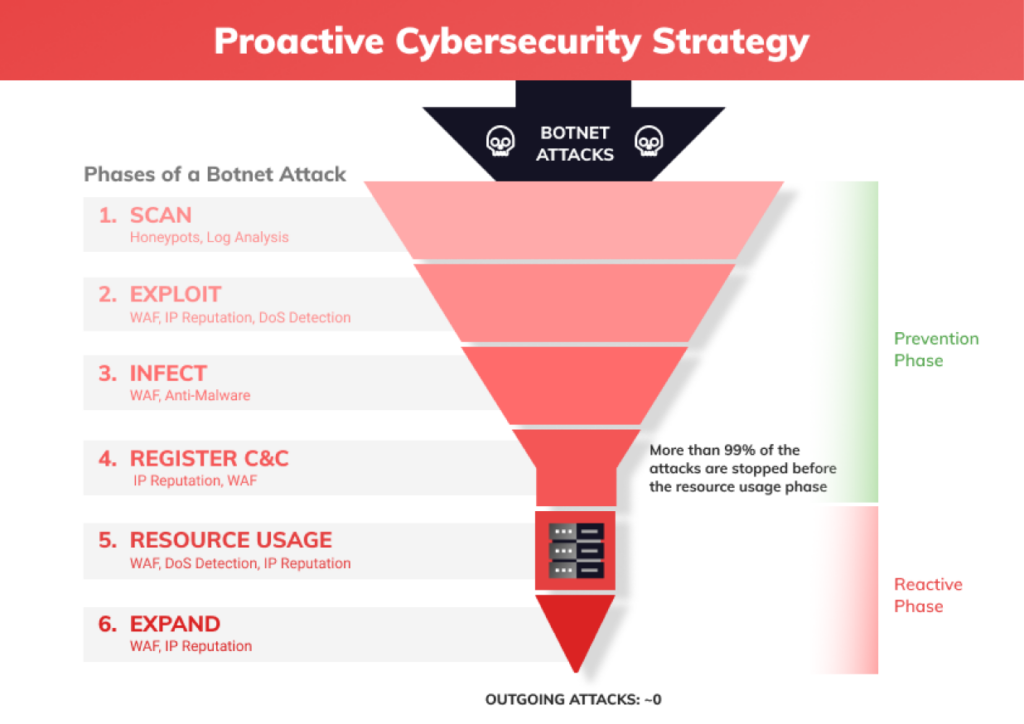
In the first four stages, while you are in the prevention phase, you can stop 99% of the incidents. You can block these botnet attacks with different proactive actions before they reach your server.
Because technology is constantly changing. Hackers are always looking for new vulnerabilities to exploit, and the best way to keep your systems protected is by staying up to date with industry security measures.
And one of the best ways to adopt a proactive cybersecurity strategy is by following popular cybersecurity frameworks, like the NIST framework we mentioned earlier. These frameworks help organizations maintain an up-to-date cybersecurity strategy that keeps up with the speed of business.
Examples of proactive processes include:
Some reactive processes include:
As you can see, these reactive processes are also an essential part of any good cybersecurity strategy. But a reactive mindset neglects preventative measures, focusing solely on what happens after a threat occurs––a common pitfall that leads to cyberattacks.
Now that we’ve looked at what a proactive mindset is, let’s talk about its benefits.
For starters, a proactive strategy is more efficient than a reactive one. Responding to cyberattacks costs a lot of time and money. But proactive strategies focus on preventing cyberattacks from happening at all. That means you don’t have to spend money paying security experts to perform cyber forensics – because no attack occurred.
And that leads us to the next point. Cyberattacks are expensive.
Not only will you spend money identifying and fixing your vulnerabilities, but you also have to worry about:
Simply put, cyberattacks can deplete your profit margin and erode your customer lifetime value.
But being proactive can improve the services you offer customers. When hackers attack your systems and drain your resources, you can expect…
Proactivity can reverse these metrics by improving your customer experience.
That’s exactly what happened with Swedish hosting company Miss Group when they turned to BitNinja for help with their cybersecurity. After the company adopted a proactive mindset that focused on prevention (and not just response), they saw an immediate drop in:
This not only meant they devoted fewer resources to putting out cybersecurity fires, but it also meant Miss Group’s customers were happier with their services. We do know happy customers translates to more money.
After everything is said and done, prevention is always cheaper than responding to threats.
Before you can perfect your cybersecurity strategy, you first need to identify the areas to improve.
The biggest indicator that you’re stuck in reactive mode is constantly spending your time responding to attacks. If your security teams spend the bulk of their time fixing security incidents, you’re not being as proactive as you possibly could be.
Another red flag that could mean your strategy is too reactive is relying on too many best-of-breed security tools. Why? Because companies often invest in these solutions in response to a cybersecurity incident. This can lead to further problems later.
Despite how good a best-of-breed solution is, there’s always the chance it won’t be completely compatible with your other security solutions – especially if you’re mixing on-prem best-of-breed tools with cloud services.
But this problem isn’t as common for organizations using a proactive strategy. Instead of buying a new best-of-breed solution every time they experience an attack, proactive people bake their cybersecurity strategy into their business model. The solutions they purchase and the workloads they build are all planned with their cybersecurity in mind.
Transitioning to being proactive can be tough but having the right layered technologies in place can ease the pain. That’s why we’ve included this checklist to help you make the jump.
This checklist will help you adopt our mindset that keeps you better protected from hackers constantly looking for new vulnerabilities to exploit.
Good cybersecurity is already evolving on the pillars of proactive strategies and technologies that currently provide predictive and prescriptive insights to thwart malicious attacks in real-time.
Some solutions are starting to use the power of artificial intelligence to recognize patterns of suspicious behavior considerably faster than SOC teams can mitigate the attacks.
Information-sharing about cyber threats between servers can make servers, leading to business continuity for hosting providers and end customers alike.
Becoming more proactive can provide a positive impact on both top and bottom-line margins. This is because a stronger cybersecurity strategy means:
In other words, the time and money you invest in creating a good cybersecurity strategy helps you retain a greater number of customers - which means more sustainable financial results for your hosting business.
We believe that although AI is in its infancy, in the not-so-distant future AI-based ecosystems/platforms will provide Security-as-a-service that will be able to harness a lot more insight from security data. Companies like ours will take the weight of proactively defending your business through delivering an all-in-one, real-time protection service to your server assets.
The data from such an ecosystem will provide insights for web hosting providers far beyond cybersecurity threats. It will provide performance metrics of server clusters, detect consistent bad actors, and help monetize your customer base by identifying those customers with weak website security and offering premium solutions, all with the power of automation.
Let's make the Internet a safer place together!

George has more than 16 years of experience in the web hosting industry and owns Web-Server, the second-largest web hosting company in Hungary. He is a frequent speaker and writer on cybercrime topics. George has made speeches at several cybersecurity conferences, such as HostingCon, Codemash, and CloudFest. He often hosts webinars and has also written an e-Book, “The Art of Server Protection".




