Two days ago storm clouds of cyberwar has reached our server from Argentina. In this article, we will share you some details about the attack.
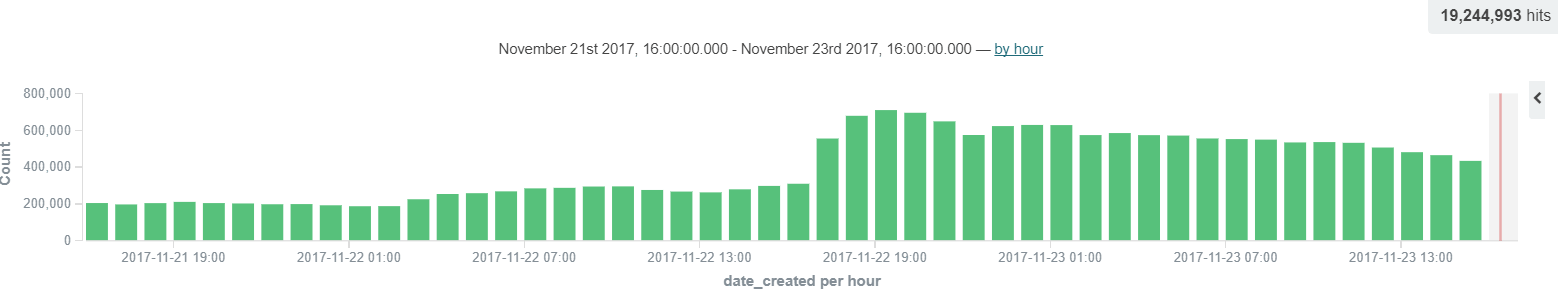
22nd November started as a usual day. Until the afternoon nothing strange happened, then at about 5 o’clock a heavier request flood reached our servers, which has been increased until 7 o’clock, and stayed really high. As you can see on the chart below, the average request number has been doubled compared to numbers from a few hours before and even tripled compared to the result from a day ago.
The numbers are decreasing, because lots of the IPs reached the limitation of blacklist, and they are not able to reach the BitNinja protected servers at all.
(If you're not familiar with BitNinja's lists, on our documentation page you can grab a lot of essential information about the operation of our IP reputation system and the different kinds of lists.)
They are simple Telnet port scannings. 🙂
In our earlier blogpost you can read more about these scans and about the reason why they are especially harmful.
Because of the request pattern, the time gap and a huge number of dynamic addresses, we think the backbone of this botnet mainly consists of routers and other IoT devices. And with high probability, it was caused by a variant of Mirai botnet, because as you know, these infected devices are often captured by Telnet Port Honeypots as well.
Nowadays the top 3 attacking countries - before the Argentine botnet - were:
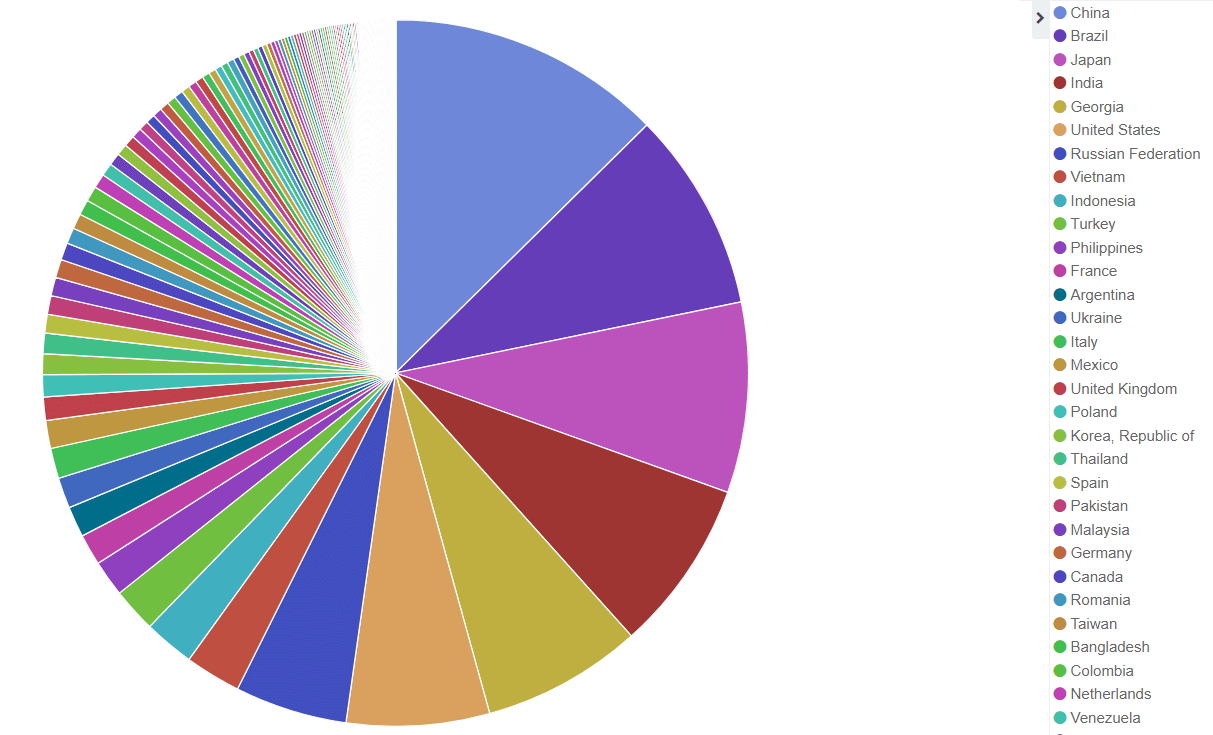
(Time range 21st 4 pm to 22nd 4 pm.)
During the storm, the top of the list has disheveled.
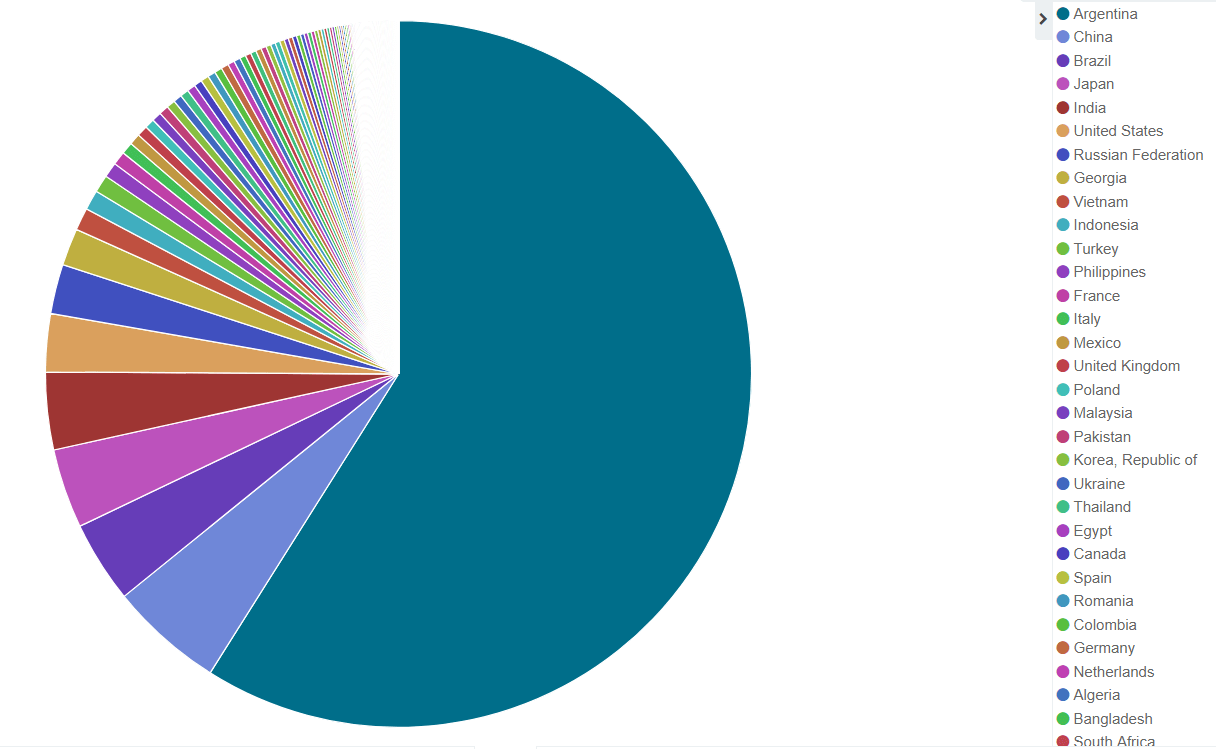
(Time range 22nd 5 pm to 23rd 4 pm.)
BitNinja provides a solution which enables you to defend your devices from these attacks without any manual intervention
.
If you would like to avoid a similar attack, we encourage you to test our 7-day free trial. 🙂




