Cryptocurrencies changed the world very quickly. It greatly impacted several things, and cybersecurity is not an exception. The most common cyberattacks on cryptocurrency blockchains are mining attacks. But what is blockchain? And how can you mine cryptocurrency?
Blockchain is the distributed ledger that contains block value, hash, timestamping, cryptography, consensus algorithm, and peer-to-peer network that provides decentralized, transparent, and cyber-secured services without the involvement of a trusted third party. The model of Cryptography was combined with blockchains and other technologies to create modern cryptocurrency by Nakamoto in 2008.
The launch of the cryptocurrency "Bitcoin" in 2009 attracted the world to blockchain technology. The dramatic developments and advancement in blockchain technology enable the numbers of blockchain-based applications in the financial sector, healthcare, e-signature and document management system, digital bonds, remittance, crowdfunding, smart contracts, IoT, and security services.
In cloud base and shared hosting services, users and devices are authenticated, identified, and connected through cloud servers.
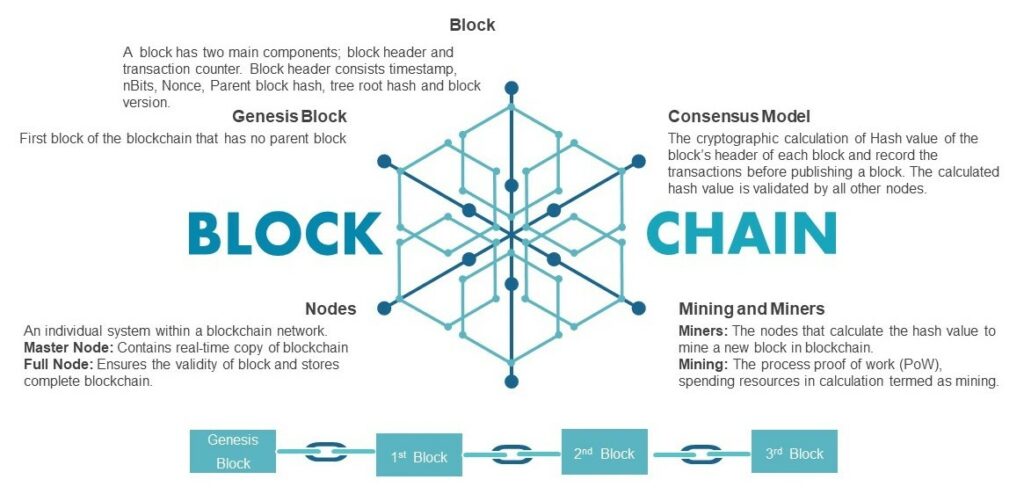
Figure: Components of Blockchain
Cybersecurity, confidentiality, and integrity of the data are still the prime concerns of cloud users and providers. There are many challenges in shared and cloud servers like costs and capacity constraints, downtime and unavailability of services, and risk of manipulation of data.
The blockchain features of decentralized access, immutability, verification, and cryptographic identification have eliminated many cloud services drawbacks. However, the rapid growth of blockchain and cryptocurrencies opens the doors for cyber-attacks.
The proof of work (PoW) is a consensus model where transactions are recorded before publishing a block by calculating the hash value of the block's header of each node. The PoW involves very complex cryptographic algorithms and complicated mathematical computations.
The PoW requires the calculated hash value to reach the target value. Once the target value is achieved, the block is published, and all other nodes validate the acceptability of the hash value.
The nodes that calculate the hash value are miners, while the procedure of PoW is termed is mining. In PoW consensus, miners have to do intensive work and computer calculation to give proof. The miners spend resources (computing powers) to mine a block. In return, they are rewarded with cryptocurrency for their effort.
Malicious crypto mining on the blockchain network is a major concern, as the miners hack the computer to utilize the computing power and resources to mine for cryptocurrencies or steal the victims' wallets.
The PoW and mining require too many resources and consumer energy. In crypto-jacking, they utilize victims' resources; the victim contributes the PoW while the cryptocurrency rewards go to the attacker.
The hackers have done the mining on victims' computers to avoid the power overhead and to have proof of work. They make "mining pools" to work collectively to generate more blocks.
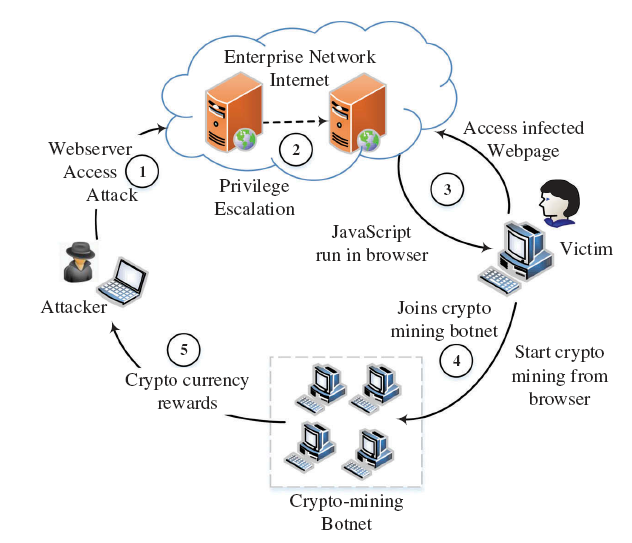
Browser-based Crypto Mining Attack
Once they achieve 51% computing power, then they take control of the attacked blockchain. The purpose of mining attacks is to get over 51% computing power to find the Nonce value quickly. By doing this, the hacker can get the authorization to determine which block is acceptable or not.
When the attackers gain over 51% of the networks' hash rate they can rearrange the transactions to prevent the other miners from computing the blocks.
The attack to achieve over 51% of computing power was in a report in June 2018 on famous blockchain-powered cryptocurrencies like Bitcoin Gold, Monacoin, Verge, Zencash, and Litecoin cash (Source).
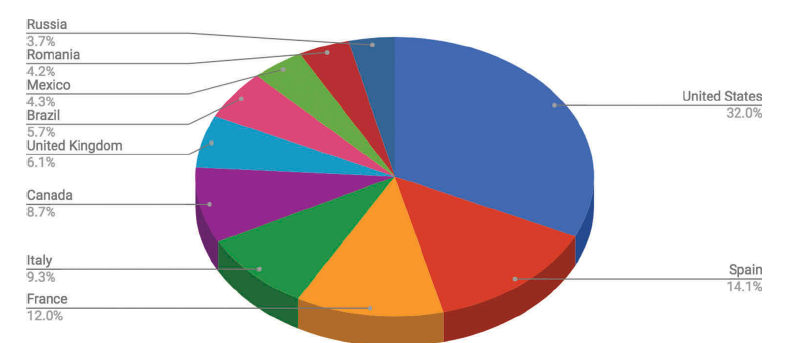
Top 10 countries exposed to browser-based mining attacks (Source)
The longer mining rounds consists of more share contribution in a mining pool. The pool hopping occurs due to the rational mining behavior of the minors.
The rational miners do the mining only when the expected reward is higher and leave the mining process when the reward is lower. Rational miners aim to enhance their rewards by adopting a pool hopping strategy, while honest miners lose their deserved profits.
Stale blocks are the blocks successfully mined but unaccepted in the current best blockchain.
Stale blocks are created in public blockchain due to race conditions where two or more miners computed the valid hash value; the blockchain accepts the (only one) winning block and rejects the others. The unaccepted and unattached valid block turns into a stale block.
The selfish miners create their private block to obtain a longer chain in a public blockchain, leading to a block race between the honest miners and selfish miners.
In the initial stages, most networks accept stale blocks, but they later reject them because of a longer chain of attackers that excludes the stale block.
To sum up the mining powers and work collectively, the miners make a "mining pool". Every member of the pool must submit their PoW to the pool administrator to show their efforts in solving a block.
The attackers join the mining pool for truthfully mining the blocks, but they never publish their successfully mined blocks.
The withholding mining attacks occur when hackers withhold important information and share partial proof of work with the administrator. The withholding mining attacks withhold and delay the block submission permanently in the network.
The attacker earns the rewards at the expense of the honest miners of the pool doing no useful work for the pool. The overall earning of the pool remains the same, but the attacker gets more incentives than honest miners without consuming power on computing.
The aim of Denial-of-services (DoS) is to prevent the system from providing services to the users.
DoS mining attack on the blockchain is the attack on the PoW consensus to build a longer chain than minority competitors. Attackers control most of the mining power to infringe the assumptions of PoW protocols. It makes a DoS attack by ignoring the blocks of minority and generating empty blocks.
By making the DoS attack, the chain of hacker grow faster than any other chain (despite having empty content) and becomes the main chain. The hackers make mining pools together to mine more blocks and share the expected reward.
This manipulating mining behavior of selfish miners reduces the revenue of honest miners. As the group of miners acquires the significant hashing power, they invalidate the ongoing transactions, prevent honest miners from mining and adding their mined block in the network, and cause failure to the network.
Blockchain provides unmatchable cybersecurity and integrity of data as compared to centralized services. The experts have given special consideration to counter the mining attacks.
Algorithms are proposed and implemented to deters selfish mining and encourage fair mining practices effectively. Mine attackers can be detected by string pattern, blacklists, CPU utilization, and drive-by mining solution like the minesweeper strategy.
It has been concluded that the mining attacks against the blockchain can be detected and cannot withstand future defense systems of blockchains. Except for the mining attacks, no other major cyberattacks on blockchains have been reported.
Defend your servers against crypto-mining-related cyberattacks with BitNinja. Cybersecurity is not optional anymore. It is a must! If you haven't tried BitNinja yet, don't forget to register for the 7-day free trial! No credit card is needed!
We are always happy to help you! If you have any questions, check out our Knowledgebase, feel free to ask at info@bitninja.com, or you can even reach us on the Dashboard chat!
Let's make the internet a safer place together!




