100% server uptime… Every hosting company is under pressure to deliver top-level metrics as per agreed service-level agreements (SLAs). Nowadays, there are countless service providers meaning customers will choose the one which grants reliability. So, what happens when a website or service is inaccessible? It’s always painful for the website owner, the visitors, and the hosting company. There could be many reasons behind it, but maybe the most annoying is when it happens because of Denial of Service DoS attacks.
In this article we will expound more on the meanings of DoS, types, and how to protect against it.
DoS stands for Denial of Service. It’s a type of attack that could render web servers unresponsive – meaning they won’t be able to serve HTTP requests. So, users can’t visit web pages hosted on them. Hackers achieve this by overwhelming the web server’s resources by issuing many connections all at once.
Maybe no lives are in danger when your website is not available, but it does cause harm to your business. When issuing DoS attacks, the hackers aim to prevent legitimate use of a service. They could do it to hurt a business rival, block banking and financial services, make the most visited websites unavailable, etc.
When an attacker mounts an attack from a single host, it would be classified as a DoS attack. In fact, any attack against availability would be seen as a denial-of-service attack.
The list of the DoS types is extensive, but the most popular DoS type, which most people fear, is the DDoS. It’s an acronym for Distributed Denial-of-Service, which is basically large-scale DoS, and it is a severe type of attack.
If a hacker uses many machines to simultaneously launch attacks against a remote host, this would be classified as a DDoS attack. So every DDoS attack is a DoS attack, but not every DoS attack is a DDoS.
For system administrators and cybersecurity personnel, it’s hard to discern normal traffic from malicious traffic when trying to detect and prevent DDoS attacks. Botnets are used on a large scale to issue DDoS attacks against servers. Often, upgrading the bandwidth will not help because the attackers would use even more machines to attack.
More attack machines (used in botnets) are harder to track down and harder to shut down. That’s why DDoS attacks are hard to prevent.
There are several symptoms that DoS attacks can cause. The most usual signs are:
That said, some of them can also be symptoms of increased legitimate traffic. You will need to dig in deeper and find out if there is suspicious incoming traffic to your site or web service. You can use traffic analytic tools to:
Today, there are two main types of DoS attacks: those that crash services and those that block services. Now, there are many tools on the web that can be used by attackers to issue DoS attacks.
For example, Slowloris is a type of denial-of-service attack tool. It tries to keep many connections open to the target web server and keep them open for as long as possible. A Slowloris attack sends partial requests and never finishes them. The program will periodically send HTTP headers but will never complete them, so the servers keep the connection open, filling their maximum concurrent connections pool.
There are denial-of-service attacks, where the aim is to slow a service down. It is called a degradation-of-service DoS attack. For example, the web service will be available, but the webserver will fulfill the requests very slowly because of the high resource usage caused by the DoS attack.
DoS attacks target different layers of the networking system. Using the Open System Interconnection (OSI) Model, we can also classify DoS attacks into three broad categories:
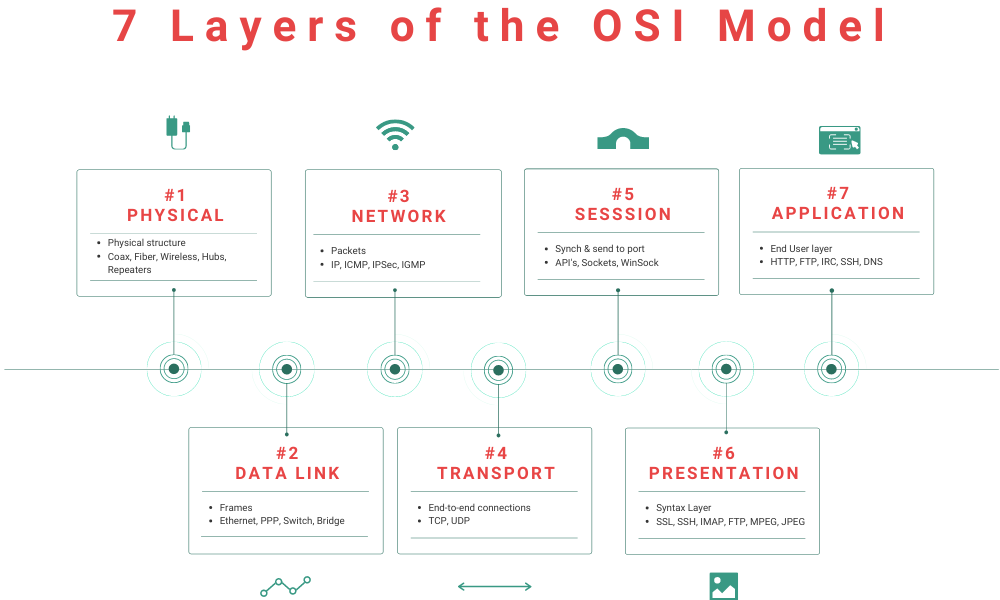
As the name suggests, these ones target the app itself (Layer 7 of the OSI model where HTTP GET and POST requests are handled).
They are the most common and the most difficult to stop. A good example is what is known as an HTTP flood DoS attack. They are hard to detect because it is difficult to differentiate between legit and rouge traffic.
Protocol attacks target network infrastructure like server resources and firewalls (Layer 3 & Layer 4 of the OSI model). Some examples are Smurf DoS, Ping of Death, SYN flood.
These types of DoS attacks are usually launched in conjunction with application-layer attacks. They usually target the bandwidth of a network or services in providers and enterprises. Some examples include ICMP flood, UDP flood, IPSec Flood, Reflection Amplification attacks.
The number of DoS attacks hasn’t just been growing over the past few years. They have also grown in sophistication. We experienced a massive increase in the number of DoS attacks in each quarter of 2020 compared to the same quarter of 2019, and in 2019 we also faced more DoS attacks than in 2018.
Again, the barrier for execution has been lowered with the availability of tools and an increased reliance on online services. DoS attack volumes are expected to keep rising and evolving in the coming years, according to a forecast by the Cisco Annual Internet Report, 2018-2023.
The surging number of cyberattacks has a lot to do with financial motives, which happens to be the primary goal of a DOS attack. A DDoS attack can lead to serious business disruptions, with the ripple effect being financial losses, loss of consumer trust, and a damaged reputation. It is estimated that a small business could lose up to $120,000 in a DoS attack.
The attackers might even execute an attack and follow it up with an attempt to extort cash from your business. This is otherwise known as a Ransom DDoS (RDDoS) attack.
According to a NetScout Threat Intelligence Report, DoS attackers tend to target connectivity and data providers. Most attacks target their infrastructure as well as consumers.
New data also shows that the games and gambling industries are becoming major targets for DoS attacks. This has also been attributed to financial motives, with some malicious players keen to circumvent the systems to win big.
BitNinja continuously monitors the number of connections on your server. If too many concurrent connections are detected, BitNinja will automatically add the IP address to the blacklist for 60 seconds to ensure that all the connections are blocked from the attacker's IP.
After that, the IP address will be placed to the greylist.
BitNinja utilizes the IP reputation module to prevent DoS attacks as well. The database has historical information about more than 100 million IP addresses. Our greylist makes the IP management more flexible and provides a more convenient way to handle false positives, while still blocking potentially malicious requests.
Greylisted IPs can be delisted by valid human visitors automatically by the Browser Integrity Check (BIC) or manually by completing a CAPTCHA.
BitNinja DoS Detection also works in conjunction with our AntiFlood module. When there are recurring DoS attempts, the IP will be blacklisted for a longer period of time.
The default threshold guarantees a low false-positive rate and also effectively blocks DoS attacks. This threshold can be configured on each port, and for inbound and outbound connections as well.
BitNinja also uses the Log Analysis module called SenseLog to ban malicious requests. There are typical attack patterns, for example, malicious requests often come from really old user agents, e.g., Mozilla/5.0 (Windows NT 6.0; rv:34.0) Gecko/20100101 Firefox/34.0
There are many reasons why the BitNinja DoS Detection module is unique and better than other solutions:
This image shows how a DoS attack looks on the BitNinja Dashboard. This malicious IP address was targeting the open 80 port of a victim’s web server.
A large number of these IP addresses are infected machines that can be used as part of botnets issuing DDoS attacks.
A network-layered DDoS (SYN flood, ICMP flood, UDP flood) is designed to overwhelm the network devices and this attack cannot be blocked on the server-side.
However, BitNinja provides indirect protection against DDoS. By constantly updating our global list of malicious IP addresses, most botnets are already blocked by BitNinja. Usually, the same botnet IPs are used to launch DDoS attacks, so our system will automatically block their requests.
BitNinja blocks DoS attacks on several protocols: HTTP, FTP, POP3, IMAP, and any other TCP-based DoS. By default, the following ports are monitored: 80 (HTTP), 25 (SMTP), 53 (DNS), and 22 (SSH). You can also customize the ports in the module’s configuration.
When a server is infected, attackers can target other devices with DoS attacks via a backdoor on your server. This consumes your server’s resources and puts your server at risk, so it needs to be stopped.
DoS attacks can have very serious consequences, and of course, nobody wants to see their servers down because of such attempts. Cybersecurity is not optional anymore. It is a must! If you haven't tried BitNinja yet, don't forget to register for the 7-day free trial! No credit card needed!
We are always happy to help you! If you have any questions, check out our Knowledgebase, feel free to ask at info@bitninja.io, or you can even reach us on the Dashboard chat!
Let's make the internet a safer place together!




