Let’s start with the definition. Ransomware is a kind of malware that installs itself onto an unprotected computer, encrypts some files, and asks for a certain amount of money for decryption or to not publish certain sensitive information online. It is called a denial-of-access attack and it can be very frustrating because you know that the files are there but you can’t access them.
There are two types of ransomware attacks:

The first known ransomware was written in 1989. Its name was AIDS or PC Cyborg. How did it work? It displayed a message that a certain software on the computer has an expired license and that the user must pay 189 USD to access their files again. The creator of this first public cryptoviral extortion attack promised that he would donate the money he got from this hack to fund AIDS research.
This malicious code only hid files on the victim’s hard drive and encrypted the files’ names.
The very first ransomware which used public key cryptography dates back to 1996. It was created at Columbia University for research purposes and was presented at an IEEE Security and Privacy conference.
Ransomware, or more scientifically called cryptovirology attack or cryptoviral extortion, operates with the use of public and private keys for encryption. At first the hacker generates a key pair, places the public key in the malicious software, and releases it. The second move is for the malware to generate a symmetric key and to encrypt the user’s data with it. The public key is used for encrypting the symmetric key.
But what is this symmetric key we are talking about? Symmetric-key cryptography algorithms use the same keys for encrypting plaintext and decrypting ciphertext. These keys can be identical or there may be simple transformation.
Plaintext is the input of encryption algorithms. A message that the sender wishes to transmit.
When plaintext is encrypted with an algorithm called cipher, it becomes ciphertext. Ciphertext is encoded information.
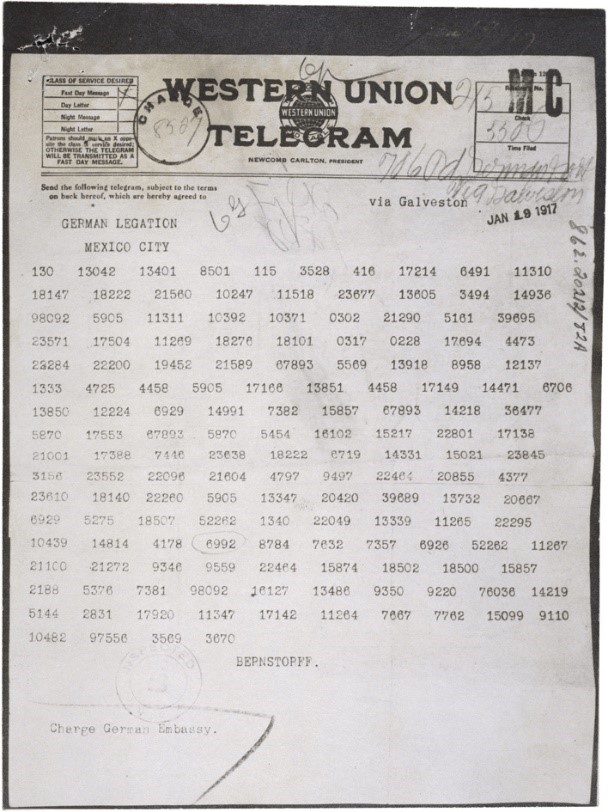 |
 |
|
1. Ciphertext
(Zimmermann Telegram)
|
2. Decrypted plaintext
of the Zimmermann Telegram
|
After this, the malware displays a message in which the hacker explains how to pay the ransom. The message also includes the asymmetric ciphertext. If the victim wants to access their data again, they must send the ciphertext and the demanded amount of money (bitcoin, wire transfer etc.) to the hacker.
Finally the attacker deciphers the asymmetric ciphertext using his private key and sends the symmetric key to the hapless user. And if everything went well, the victim will decipher the encrypted data with the symmetric key and get their files back.
The two most common ways are opening malicious email attachments and visiting compromised websites. Like with any other kind of attack (and generally when using of our personal or workplace computer), caution and proper protection is always advised.

Hackers usually demand some form of electronic payment from their victims. It can be sent using a wire transfer or bitcoin. One news report states that sometimes the attack is so sophisticated that the attackers even communicate with their victims like a legitimate company would to its’ customers.
In one news report from PBS News Hour, an elderly lady’s computer was locked by ransomware and the hackers demanded payment in the form of bitcoin. They also created an informative help page about this type of money and linked useful websites describing bitcoin. The report stated that the attackers operated almost like a well-built customer service. In the end, the family paid 500 USD to the hackers, but since the payment was two days late, they had doubled the price to 1000 USD.
Nowadays more and more reports talk about ransomware attacks. They are targeting hospitals, public transportation systems, university computers, halting the day-to-day operations of important medical and government facilities, police departments, education services, and so on.
In the case of Hollywood Presbiterian Hospital in Los Angeles, the malware rendered all patient files inaccessible and the medical personnel were forced to use pen and paper for record keeping. Their computers were offline for more than a week.
The hackers demanded 17,000 USD for ransom. Eventually the hospital paid the price and the FBI started investigations. In the end, no patient files were compromised, but the attack certainly disrupted operations for several weeks and demanded a high price too.
Do not worry about the intrusion of cybercriminals who would like to cheat you out of your money! Install BitNinja on your server and monitor how it drops the malicious packages sent from botnets of hackers.




