After the “Hello, Peppa!” zero-day botnet, our Attack Vector Miner detected another zero-day vulnerability.
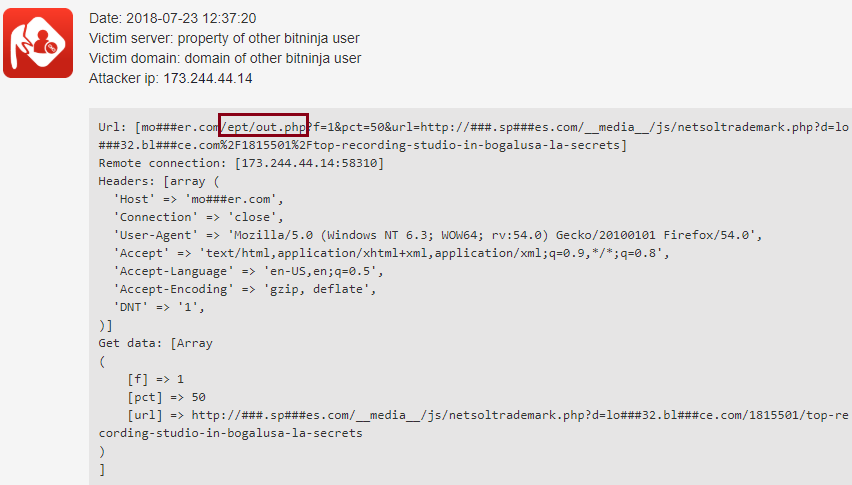
Some vulnerable websites contain an /ept/out.php file, which can work as an open proxy. That’s why the attacker scans the /ept/out.php file. Let’s see an example:
The number of these attacks started to increase on July 11th, and as we can see in the diagram below, the botnet’s activity is slowing down now.
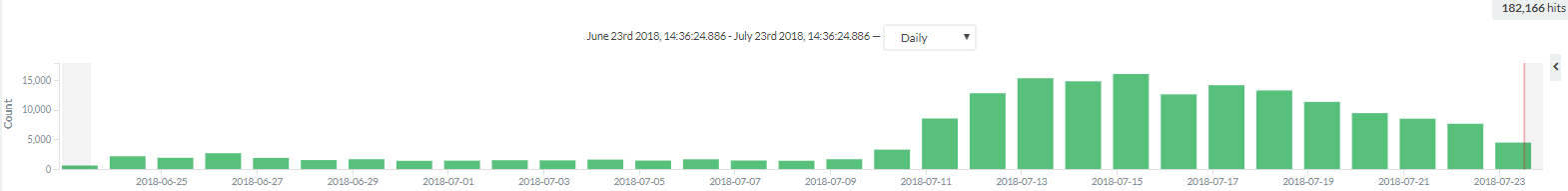
During the peak time, we experienced 15.000 attacks per day and most of them targeted only one of our customers.
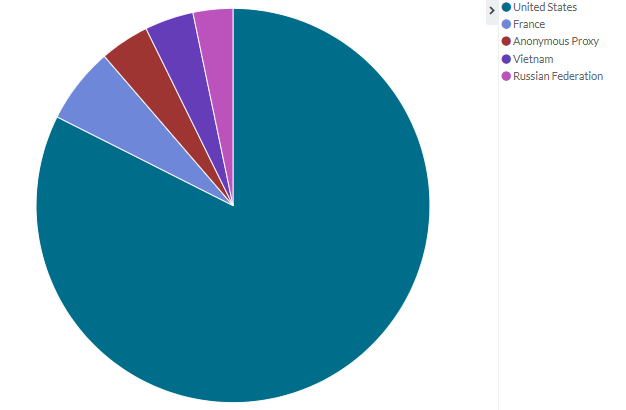
Between June 23rd and July 23rd there were more than 180.000 /ept/out.php scans. More than 80% of them came from the US.
Here’s a pie chart regarding the top five countries where the most /ept/out.php attacks originated from:
The other attributes of the attacks (e.g., IP, User Agent, etc.) are varied, so it’s not worth analyzing the logs according to them.
As you can see, BitNinja is a successful weapon against this zero-day botnet. With BitNinja Pro, you don’t have to worry for even one minute. 😉
Stay safe our Ninja Fellow!




