Security is crucial, either on the internet or out of the world of the internet. Everyone is concerned about cybersecurity, particularly the webmasters who host their website on a shared web hosting server.
Implementation of the best security measures is tough in a shared web hosting environment, and here’s why:
But, you don’t need to worry because we are here to help you. There are ways to prevent risk and to create a safe environment for your shared hosting company.
Before understanding how to prevent cyberattacks, we need to look at different ways to identify and know you are being attacked. Hackers have different techniques to get into your system. So, here are some of the most common symptoms you can identify quickly.

Lots of sites hosted on your shared hosting environment not loading at the same time is a potential signal of increased cyberattacks. This can result from a DoS attack on your web server. It is not easy to defend as the hacker uses a network of machines to implement this (aka DDoS attack).
High server load and memory usage are also the signs of a DoS Attacks.
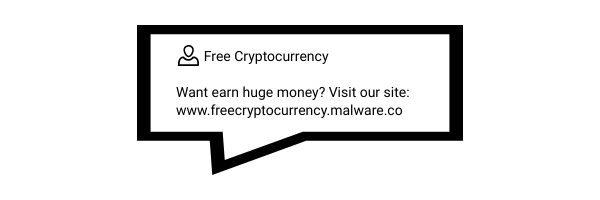
If you find many unwanted forum posts and blog comments on your website it because you are a target of spambots.
Spambots (or spammers) abuse web-based forms to post unrequested advertisements. Most of these messages simply contain links intended to boost search engine ranking.
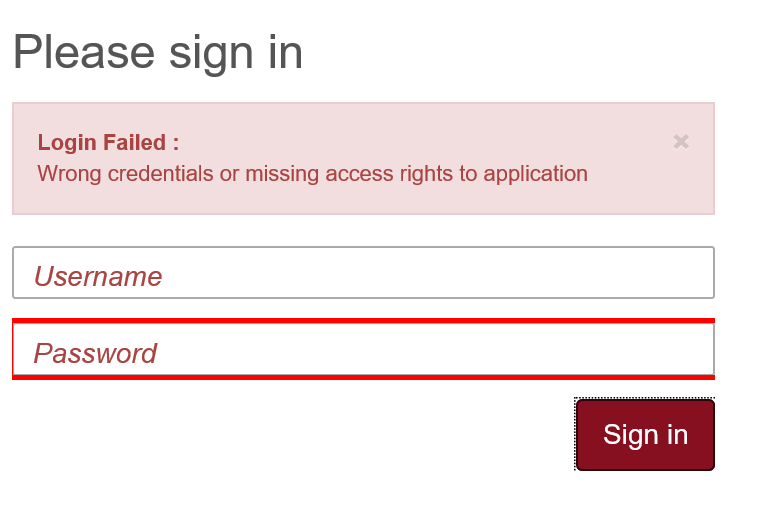
When an unusual number of users are locked out from signing in is the signal that your server is under a brute-force attack.
Malicious botnets often use dictionaries of common names and phrases to find the right username and password combination to hack an account. They systematically check many possible login credentials until they succeed. This type of attack isn’t very elegant and relies on making many trial-and-error attempts to log in.
The most popular targets of brute force attacks are email accounts, WordPress/Joomla/Drupal admins, FTP, and SSH access. Typically, these malicious botnets use many different IPs to carry out their attacks.
Prevention of cyberattacks is easier when you can identify them. However, in a shared hosting environment, it becomes difficult to implement security measures as all of the hosting accounts won’t be using the same CMS running on the same services.
Also, every hosting account has a different configuration setup and uses different services on the server.
Shared hosting requires the best security measures implemented on the server. I bet you don’t want your technical support team working to clean websites from malware. It results in huge support and technical costs to clean malware and fix customer websites, and last but not least, data leakage can cause serious reputation loss for your company.
Allowing users to use 2FA on their hosting account is a great idea to prevent unauthorized access to your services, especially useful against brute-force attacks.
If you're implementing it in a shared hosting environment, first you have to make available the 2FA option for the users and then make them somehow to set it up on their account. Write a newsletter or a blog post for them on how to do it properly.
It keeps your customer’s hosting account secure even if their password or any personal information is compromised. Furthermore, don’t let the hosting account owners use a weak password for their account.
The Log Analysis module automatically recognizes the most common log files on your server and starts to analyze them in an efficient and resource-friendly way.
This module will immediately block brute force attacks and many other attack types, including SQL injection, directory traversal, spamming attempts, WordPress user enumeration attack, reflective DDoS via xmlrpc.php, and more.
BitNinja Log Analysis doesn’t require configuration and runs silently in the background, monitoring malicious IP addresses. When this module detects a malicious IP, it is automatically greylisted by our real-time IP Reputation module. We constantly update our IP rules and continuously monitor log files, ensuring you always have the latest protection on your server.
DoS attack (Denial-of-service) is one of the most common types of cyberattacks, and they are easy to identify. The purpose of this attack type is to stop a service. The symptoms are high server load and memory usage or slow, sometimes inaccessible services.
When the DoS protection tool detects an attack, if there is a lot of connections from a single IP. The DoS detection tool’s threshold should be configurable on a per-port basis.
Most of the time, the target protocol is HTTPS. However, the attacker can attack various servers with different protocols such as SSH, SFTP, FTP, SMTP, etc.
BitNinja has a built-in module for monitoring current active connections and interfering in case of a potential denial of service attack. If there are more than 80 connections from a single IP, BitNinja detects it as an attack.
Our default thresholds and greylist provide the perfect balance between a low false-positive rate and maximum protection. The 80 threshold can be configured on a per-port basis. You have to create a config file if you want to change the default thresholds.
BitNinja's DoS Detection module blocks not only inbound attack attempts but also outbound DoS. Beyond simply blocking HTTPS attacks, it blocks FTP, POP3, IMAP, and any other TCP-based DoS attack.
Websites are the main point of weakness for shared servers. Many botnets specifically target and exploit website vulnerabilities to gain control of a server and use it to launch their automated attacks.
A web application firewall is a set of rules to harden the security shield on your web application. It keeps your CMS safe from several cyberthreats such as Cross-site scripting, SQL injection, etc.
In a shared hosting environment, WAF implementation can cause some sites not to work properly because every hosting account has different services, software, or plugins. Choose a WAF that enables you to change the strictness level to block malicious traffic and allow genuine traffic to reach each hosted site.
The BitNinja WAF 2.0 operates between visitors’ web browsers and your web server. It’s a very fast reverse proxy that filters all incoming web requests, automatically rejecting any attacks.
The BitNinja WAF 2.0 makes it easy to manage all your firewall settings from one location, and you can also configure the filter level by domain. By using domain-based patterns, you can change the strictness level by domain or by URL. This unique feature is only available with BitNinja and makes life a lot easier when managing shared servers.
To keep you secure from the latest threats, we constantly patch new kinds of CMS vulnerabilities by adding new WAF rules to the rulesets. We also include automated false-positive reporting that allows you to fine-tune the settings if needed, and we guarantee a low false-positive rate with the pre-defined rulesets.
Cybersecurity is not optional anymore. It is a must! If you haven't tried BitNinja yet, don't forget to register for the 7-day free trial! No credit card needed!
We are always happy to help you! If you have any questions, check out our Knowledgebase, feel free to ask at info@bitninja.io, or you can even reach us on the Dashboard chat!
Let's make the internet a safer place together!




