At the beginning of the year we released our brand-new FtpCaptcha module, and of course, we were so excited about receiving the first incidents. However, we didn’t think that the very first logs will be such eye-catching. We detected a not so well-known botnet, and we didn’t find an article about it (only a few forum topics), so we summarized everything that you need to know about it.
This botnet is trying to upload a file named GXHLGSL.txt, which contains only this: TEST. If it was a vulnerability scanner, there would provide some description about it on the internet, but no result… So, it’s obvious that it isn’t made by a human either as the FTP CAPTCHA would be challenged successfully.
Let’s look closely to file uploading attempt from this botnet:
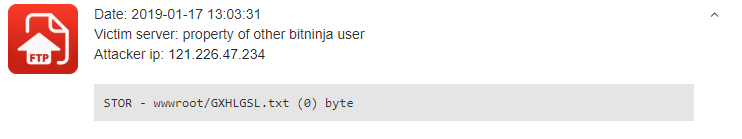 This request was captured by our brand-new FTP CAPTCHA. Do you want to learn more about how this feature works? Read more about the FTP CAPTCHA in our blog post or our documentation site.
This request was captured by our brand-new FTP CAPTCHA. Do you want to learn more about how this feature works? Read more about the FTP CAPTCHA in our blog post or our documentation site.
We dug deeper in the data, and we found that after trying to upload the file GXHLGSL.txt, this botnet scans on HTTP too to check whether the file upload was successful or not. Here is an example from one of our clients’ server:
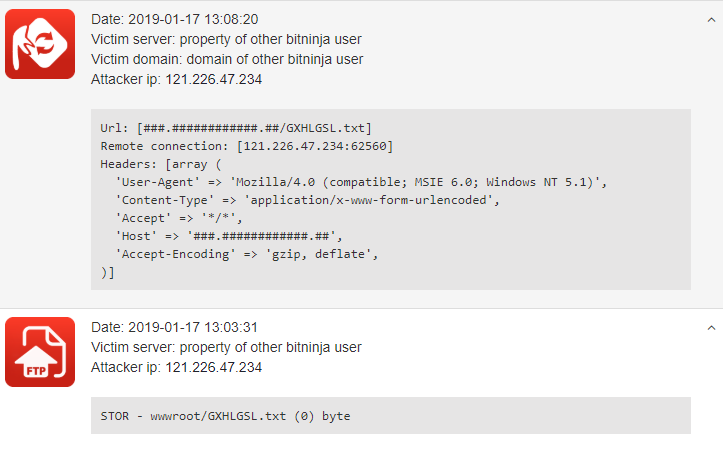
Interesting fact: Not only was the GXHLGSL.txt the only one that was attempted to be uploaded and then scanned on HTTP. A similar file is the ftpchk3.txt, but this botnet isn’t so intense.
Since the FTP CAPTCHA release, we stopped almost 700,000 attacks from this botnet; 57% were file uploading attempt (caught by BitNinja FtpCaptcha), and 43% were scanning the file on HTTP (caught by BitNinja Web Honeypots).
In this graph you can see the distribution of these attacks:
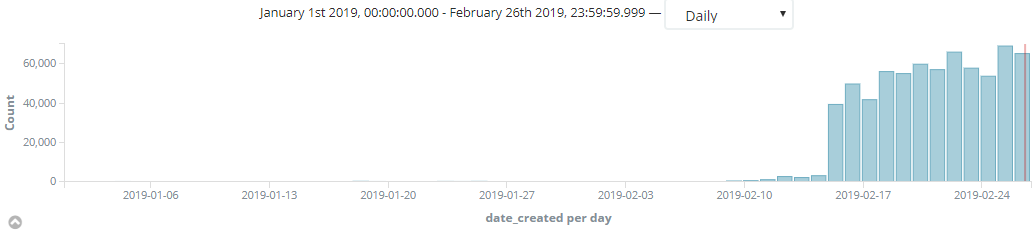
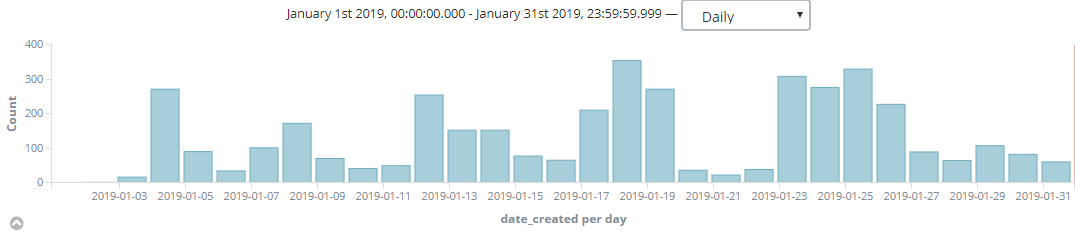
You can see that the number of captured attacks was significantly started to increase on 15th February. That was the point when the FTP CAPTCHA was enabled by default on all servers. It looks like if there wouldn't be any catch in January, but that's not true. In the first month of the year, we stopped more than 4,000 attacks from this botnet, when only a few servers were testing this brand-new module. Here you can find a chart about that period:
China is responsible for 99,4%
of these attempts, but there are Sri Lanka and Brazil in the Top 3 too.
As we could see from the chart above, enabling the FTP CAPTCHA on every BitNinja protected server was highly increased the number of stopped attacks by the GXHLGSL botnet. And guess what! It was already listed in the Top 15 attack types between the XML-RPC scan, WP User Enumeration Attack, WP Brute Force and other common attack types since then. The GXHLGSL botnet is taking the 10th and 11th place of the Top List with the FTP and the HTTP scans. Let's take a look at how the Top 15 List looks like now:
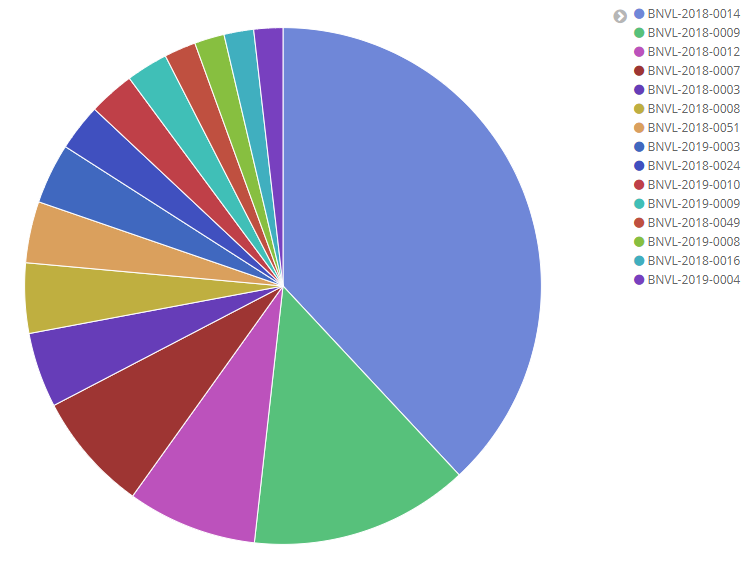
1. BNVL-2018-0014: WordPress XML-RPC Scan
2. BNVL-2018-0009: WordPress Brute-force Login Attempt
3. BNVL-2018-0012: WordPress username enumeration
4. BNVL-2018-0007: Automated WordPress Registration
5. BNVL-2018-0003: Testing for open form
6. BNVL-2018-0008: Redirect Vulnerability in WordPress's WP Login Plugin (wp-login.php) (CVE-2014-2229)
7. BNVL-2018-0051: Backdoor testing
8. BNVL-2019-0003: SSH bruteforce
9. BNVL-2018-0024: BitNinja CAPTCHA request
10. BNVL-2019-0010: GXHLGSL botnet FTP scan
11. BNVL-2019-0009: GXHLGSL botnet HTTP scan
12. BNVL-2018-0049: Backdoor testing
13. BNVL-2019-0008: SQL injection attempt
14. BNVL-2018-0016: Testing for User Enumeration and Guessable User Account (OWASP-AT-002)
15. BNVL-2019-0004: SSH brute-force attempt
The FTP CAPTCHA debuted well by capturing this very intensive botnet, so this module is enabled by default on your servers from the version 1.27.2. We talked a lot about this module in this article but don’t forget there are 9 BitNinja Pro modules which protect your servers in every phase of the attack cycle.
Haven’t tested BitNinja yet? Book a demo, and we’ll show you that stopping the cyber attacks on your servers is child’s play with BitNinja. It’s time to start kicking the hackers’ ass right now!




