We won’t stop until we have caught all of the malware around the world. With this in mind, we made some developments again in the Anti-Malware Module.
Let’s see what has changed!
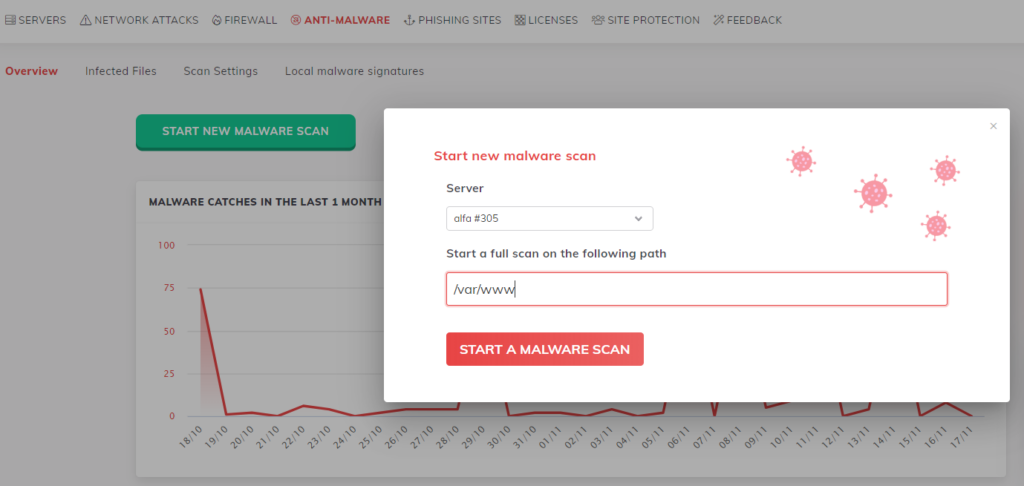
It is now much easier to start a Malware Scan. Just go to the Anti-Malware section on the Console, and you will find the “Start New Malware Scan” button. Click on it, choose the server you want to scan and write in the path below.
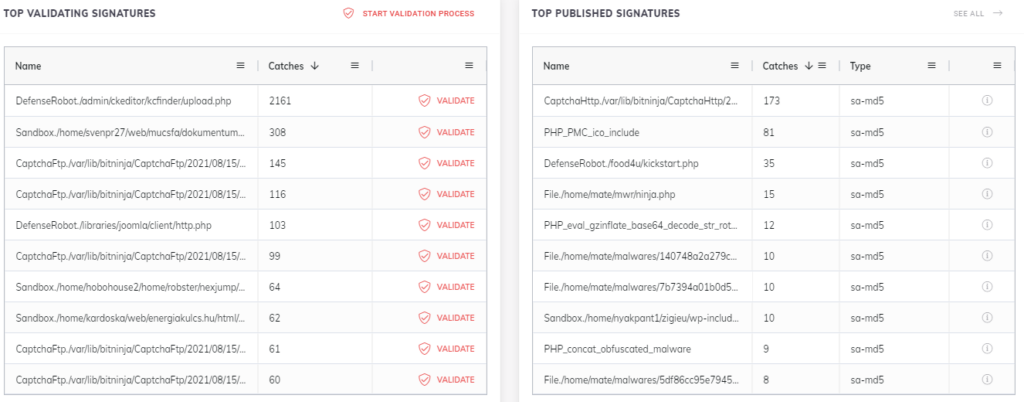
Malware signatures are displayed in the same section with the new, improved table layout. Suspicious files validation can be reached from here, so there is no need for a page reload anymore. You can also check those signatures that had the most malware catches.
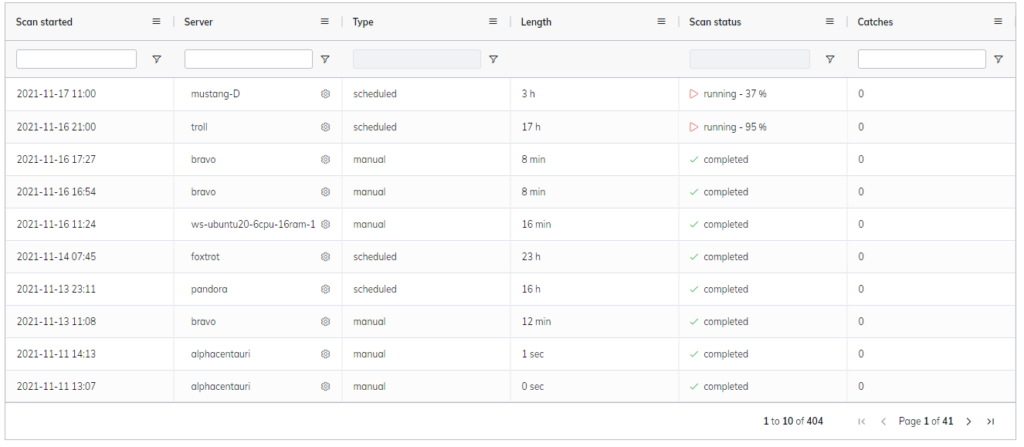
And from now on, the started and finished scans can be examined on the Anti-Malware Overview page.
As time goes by, malware injection techniques are getting more and more sophisticated, with different encrypting and forms of malware. These new methods required a new approach to the way we eliminate them, introducing: the SA-Snippets.
SA stands for Structure Analysis, which you can read more in-depth about here.
We only remove the infected, harmful part from a file, leaving the good bits untouched with this method. The great thing about this is that even if the malware tries to disguise itself by using different characters, our signatures can still recognize harmful code and clean the files.
We have cleaned over 400,000 injected malware with the new technique.
Our malware-hunting Ninjas are tireless and did an absolutely fantastic job this year.
We have seven times more global blacklisted published signatures than we had at the end of the last year. This result is also reflected in the number of our malware catches.
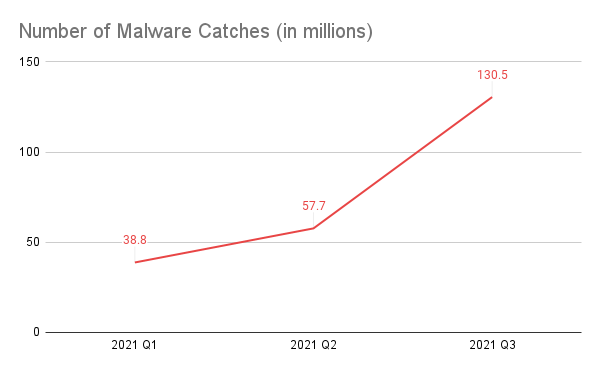
In 2021 Q1, we caught 38,8 million malware, and in the third quarter of the year, this number went up to 130,5 million.
Last year, we invented a brand new malware detection technique, the source code structure analysis. This method is a disruptive innovation that recognizes even obfuscated malware.

It creates a special structure-based signature from the source code and then does the matching on the structure. This way, no matter how hackers alter the source, the structure will be the same.
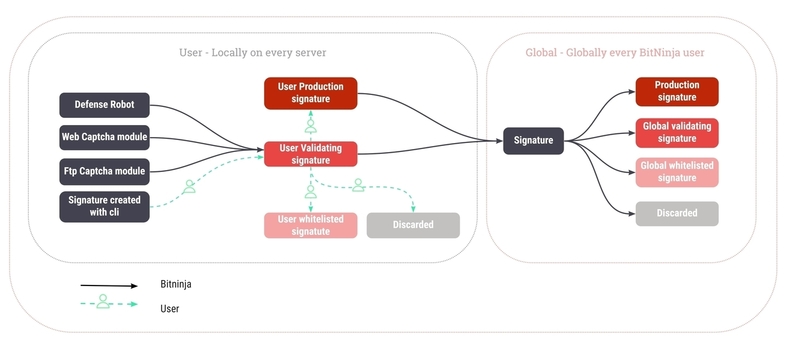
This year, we reconsidered our validating signature collecting process. We changed the Web Captcha, the FTP Captcha, and the Defense Robot modules to gather as many signatures as possible.
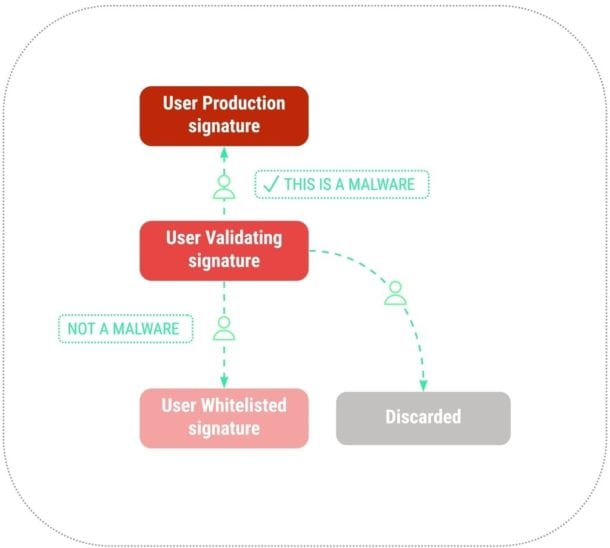
We realized that you need a more simple validation process, so we developed a new feature on the Console that closely resembles a well-known online dating service. It shows the source of the signature syntax highlighted, and you can decide whether or not it’s malware or if you are unsure about it. This way, you can publish malware and quarantine the files in one step!
Next, we also added a new module to the BitNinja system we named Sandbox Simulator. It’s a PHP emulator that runs the PHP files on the server in a safe environment and automatically analyses the file’s behavior.
It also analyzes the old PHP files on the servers. We can easily discover the most recent zero-day malware with the Sandbox Simulator, even if they are obfuscated.
We keep on going to have you the world’s best cybersecurity tool!
To learn more about the new features, visit our Documentation page, check out our Knowledge Base, or write to us directly.
Do you have ideas for new features or some suggestions on how we could improve BitNinja? Don’t hesitate to share it with us.
Cybersecurity is not optional anymore. It is a must! If you haven’t tried BitNinja yet, don’t forget to register for the 7-day free trial! No credit card needed!
Let’s make the Internet a safer place together!




